LAS VEGAS–Microsoft’s Windows 10 includes many innovative security features that are intended to help minimize risk and improve user experience. One such feature is Credential Guard, which aims to protect users against attacks. However, according to security firm Bromium, many risks remain.In a video interview with eWEEK ahead of a session on Aug. 4 at the Black Hat USA conference here, Rahul Kashyap, chief security architect and executive vice president at security firm Bromium, discussed multiple flaws his firm found in Windows 10, including Credential Guard as well the kernel code integrity feature.Kashyap explained that Credential Guard is an effort from Microsoft to limit or eliminate the risk of an attack known as “Pass-the-Hash,” where an attacker is able to access a password or credential hash and then reuse it in an attack. Credential Guard makes use of Windows 10 integrated virtualization, which Kashyap said is a step forward for security, but is still lacking in some security controls.Bromium has alerted Microsoft to the issues it found, and some, but not all, the identified risks have been patched.
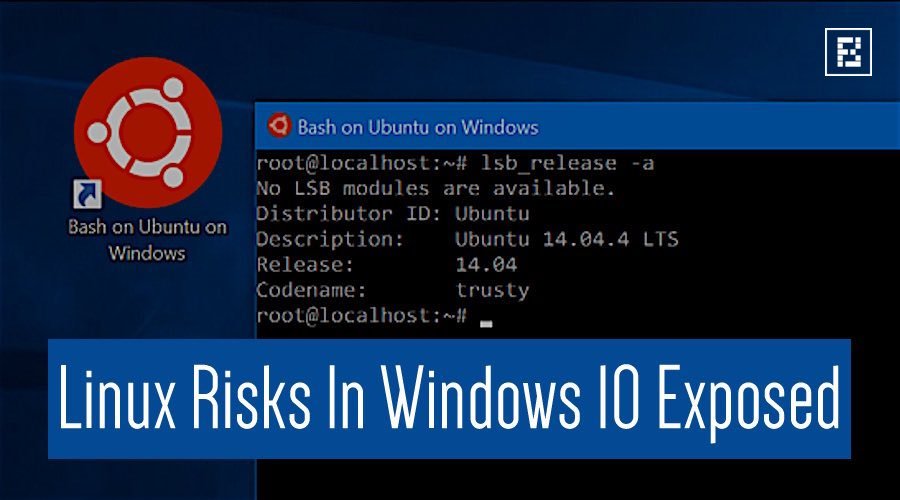
“The Credential Guard issue is tricky and will be difficult to fix,” Kashyap said. From a vulnerability perspective, Linux on Windows is not running inside of a Hyper-V hypervisor, which potentially could isolate the Linux processes. Linux is running on the raw hardware, getting all the benefits of performance and system access, as well as expanding the potential attack surface, he said. The Windows file system is also mapped to Linux, such that Linux will get access to the same files and directories.The updating mechanism inside of Linux for Windows is also an area Ionescu looked at. There is a scheduled task that can be set in Windows to run the Apt-Get Linux command to update packages for the user mode that is enabled by Ubuntu. That said, Ionescu noted that Microsoft isn’t actually using an Ubuntu Linux kernel, just user-land tools and applications.”The kernel piece is Microsoft’s own implementation and is updated via the usual Windows Update mechanism,” he said.Among the issues that Ionescu is still concerned about is the fact that AppLocker, which is Microsoft’s whitelisting service for Windows applications, doesn’t work for Linux applications. As such, if an enterprise has enabled Linux on systems, Linux apps can potentially run without first checking with AppLocker.If there are risks, Ionescu noted that a network firewall device would potentially see the traffic. He added that while users might not be able to do traditional antivirus, behavior-based security software will likely catch indicators of compromise.Although the risks exist, Ionescu said to enable the Linux features in Windows, users will need to enable developer mode and install additional packages. Ionescu, however, doesn’t expect widespread attacks as the Linux feature is still very new and not broadly deployed.”Attackers don’t usually go after the latest things where they would only impact a small percentage of the market,” he said. “But as the feature adoption grows, this might become a more attractive attack vector.”

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.