The Domino Ransomware is a new infection discovered by Daniel Gallagher and Michael Gillespie that is based off of the Hidden Tear open-source ransomware project. What makes this variant interesting is that it pretends to be the KMSPico Windows activation crack that will actually install KMSpico, but also encrypt a victim’s files as an added bonus. It should be noted that this does not appear to be the official KMSpico program, but rather a modified installer.
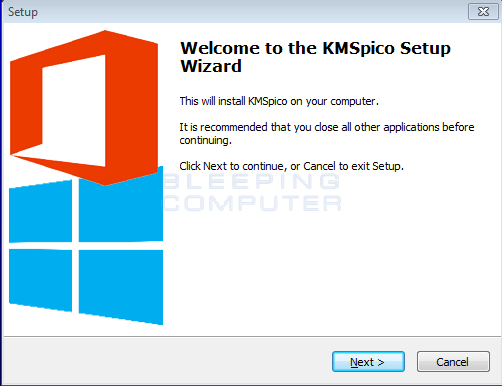
When the KMSpico installer is executed, it will extract a random named file into the %Temp% folder. This file is then executed and will extract a password-protected zip file called Help.zip. The password to this file is abc123456 and contains two files; a help.exe and a HelloWorld.exe file. The help.exe is the encryptor, which will encrypted files and add the .domino extension to them, while the HelloWorld will display a ransom note.
This ransom note is titled HelloWorld! and contains instructions on how to pay the ransom and contact the developer at 61f1e8055af3f6a672959e6b0493a2@gmail.com. Included in the ransom note is a Game of Throne’s reference of “Winter Is Coming!”, but even better there is an ascii cow!
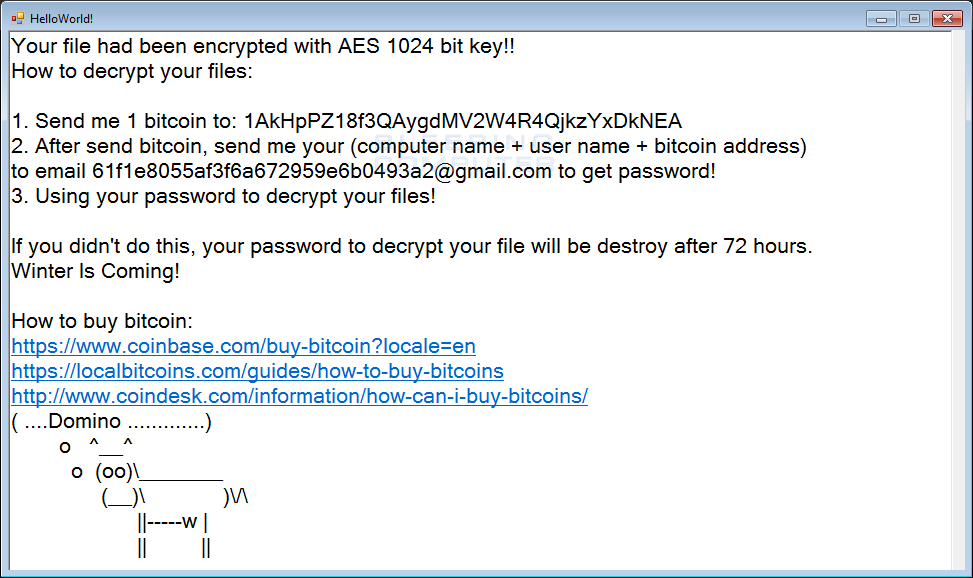
Overall, there is nothing of particular interest about this ransomware other then that its distributed as KMSpico, and even better, contains a ascii cow! I mean who doesn’t like cows?
It’s Hidden Tear, so Michael’s Hidden Tear Brute Forcer will be able to brute force the decryption key so a victim can get their files back.
Source:https://www.bleepingcomputer.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











