FBI says it’s impossible but Cambridge computer security expert proves them wrong.
Passcodes on iPhones can be hacked using store-bought electronic components worth less than $100 (£77), according to one Cambridge computer scientist.
Sergei Skorobogatov has demonstrated that NAND mirroring—the technique dismissed by James Comey, the director of the FBI, as unworkable—is actually a viable means of bypassing passcode entry limits on an Apple iPhone 5C. What’s more, the technique, which involves soldering off the phone’s flash memory chip, can be used on any model of iPhone up to the iPhone 6 Plus, which use the same type of LGA60 NAND chip. Later models, however, will require “more sophisticated equipment and FPGA test boards.”
In a paper he wrote on the subject, Skorobogatov, a Russian senior research associate at the Cambridge Computer Laboratory’s security group, confirmed that “any attacker with sufficient technical skills could repeat the experiment,” and while the technique he used is quite fiddly, it should not present too much of an obstacle for a well-resourced branch of law enforcement.
The attack works by cloning the iPhone’s flash memory chip. iPhones generally allow users six attempts to guess a passcode before locking them out for incrementally longer periods of time; by the complex process of taking the phone apart, removing its memory chip, and then cloning it, an attacker is able to have as many clusters of six tries as they have the patience to make fresh clones. Skorobogatov estimates that each run of six attempts would take about 45 seconds, meaning that it would take around 20 hours to do a full cycle of all 10,000 passcode permutations. For a six-digit passcode, this would grow to about three months—which he says might still be acceptable for national security.
He demonstrated the fruits of his labour in a YouTube video, which clearly shows him making more than the regulation number of passcode entries by switching a fresh, identical chip into a physical port he’d attached to the phone he was attacking. “Because I can create as many clones as I want, I can repeat the process many many times until the passcode is found,” he explained in the video.
Apple doesn’t readily release the part numbers or wiring diagrams for the chips and circuits inside each iPhone, but the information is easy to find online (see the recent iPhone 7 teardown). This information can be used to cleanly open the handset up and identify the location of the flash memory chip on its main board. And while NAND flash memory manufacturers have so far managed to prevent the release of any documentation on how they actually work, it’s possible to eavesdrop on their protocols and commands with an oscilloscope or a logic analyser.
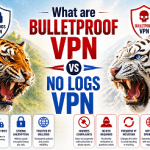
NAND memory is usually preferred to NOR memory on small devices due to its higher density and faster data-transfer rate, though it can only withstand tens of thousands of rewrites rather than hundreds of thousands for NOR, which complicates the hacking process.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.