Newt Gingrich brokered deal for moonlighting contractor to hunt for potential breach.
More records from the Federal Bureau of Investigation’s review of Hillary Clinton’s e-mail practices have been released through the FBI’s Freedom of Information Act site, including interviews with a number of individuals related to the security of the server. One of them was an employee of a defense contractor who claimed he was funded by Judicial Watch to investigate whether Clinton was hacked.
In the interview, the individual, whose name was redacted, claimed that he used the services of Dark Horse Data, a company owned by former Deputy Undersecretary of Defense for Intelligence Reginald Hyde, to search for e-mails associated with Clinton’s personal account. The company focuses on “specialized data acquisition for both US and International customers” and has provided database intelligence analysis to the US government.
The credibility of that information, however, is certainly in doubt. Hyde denied that his company was involved in any such task, telling Ars Technica in a phone interview that he “was quite astounded to learn” of the assertion in the FBI documents and saying that it was like “being asked how your day on Mars was. My company was categorically not involved in this.”
In the summer of 2015, the FBI interview report noted, the interviewee reported that a senior staff member of the US Senate Judiciary Committee contacted him “out of concerns data from Clinton’s e-mail server might end up overseas. Specifically [name redacted] wanted to determine if there was an intrusion into Clinton’s server and, if so, whether exfiltrated data fell into the hands of a foreign power”—and whether that data could endanger the Senate staffer’s sons, who were in the military.
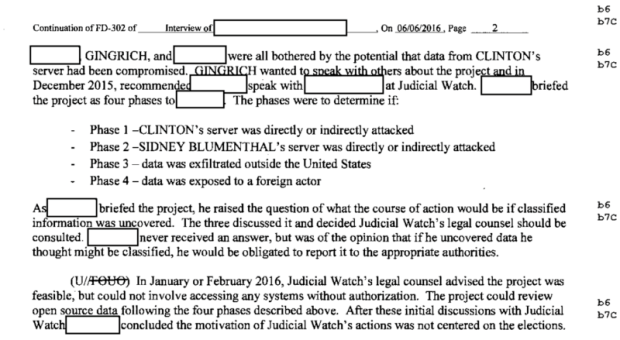
The interviewee told FBI investigators that he had told the Senate staffer that he would have to look for data that was “genuine, authentic and relevant” to determine that there had been a breach. But the staffer had no money to fund the research, so the project was brought to Newt Gingrich—who obtained funding for the investigation from Judicial Watch.
In March of 2016, Judicial Watch paid the contractor’s side company $32,000 for the first phase of the project—determining whether Clinton’s server had been directly attacked. “Judicial Watch awarded the contract to [name redacted] because they were confident he understood both the Deep Web and the Dark Web,” the interviewee told the FBI. The investigation also targeted data from Sidney Blumenthal’s e-mail account, but Clinton’s and Blumenthal’s actual e-mail services were off-limits for the search.
Some of Blumenthal’s files—but no e-mails—were found on a server in Romania, according to the FBI interview. The investigation also found an Excel file listing names of known or suspected jihadists in Libya—but part of that file was in Russian. “The file did not come from Blumenthal’s server, but contained a reference to an IP address range that included the IP address of Clinton’s server,” the FBI report recounts. “Upon viewing this file, [name redacted] became concerned he had found a classified document and stopped the project.”
Source:https://arstechnica.com

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.