Malicious ads exploited zero-day flaw in Android that auto downloaded files. Google has shut down an operation that combined malicious AdSense advertisements with a zero-day attack exploiting Chrome for Android to force devices to download banking fraud malware.
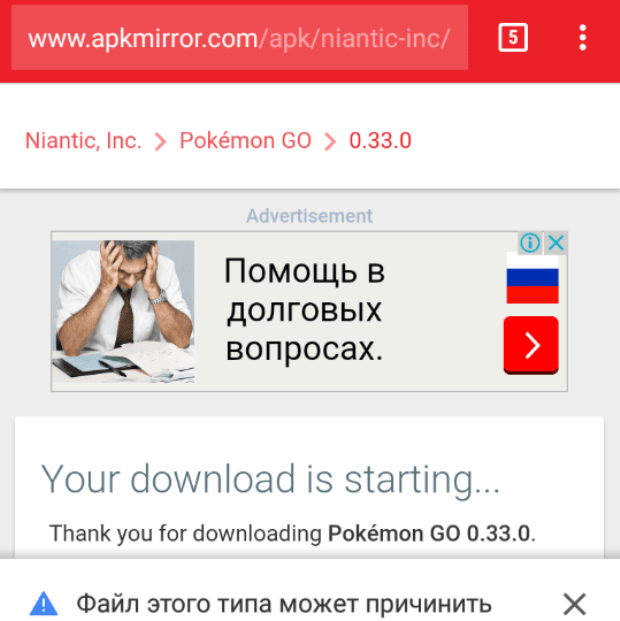
Over a two-month span, the campaign downloaded the Banker.AndroidOS.Svpeng banking trojan on about 318,000 devices monitored by Kaspersky Lab, researchers from the Moscow-based anti-malware provider reported in a blog post published Monday. While the malicious installation files weren’t automatically executed, they carried names such as last-browser-update.apk and WhatsApp.apk that were designed to trick targets into manually installing them. Kaspersky privately reported the scam to Google, and engineers from the search company put an end to the campaign, although the timing of those two events wasn’t immediately clear.
“So far, those behind Svpeng have limited their attacks to smartphone users in Russia,” Kaspersky Lab researchers Nikita Buchka and Anton Kivva wrote in Monday’s post. “However, next time they push their ‘adverts’ on AdSense they may well choose to attack users in other countries; we have seen similar cases in the past. After all, what could be more convenient than exploiting the most popular advertising platform to download their malicious creations to hundreds of thousands of mobile devices?”
A Google spokesman said a fix for the auto-download vulnerability was being tested in Chrome version 54 and was expected to be “live 100%” in version 55. (He didn’t respond to a request asking him to elaborate.) He also said an Android security feature known as Verify Apps provided warnings when people tried to install one of the malicious apps. He didn’t explain how the malicious advertisements snuck by Google security checks or what company engineers are doing to prevent AdSense from running similar ones in the future. Last week, researchers from a separate security firm named Cylance disclosed a separate malvertising campaign on Google AdWords that targeted Mac users.
Kaspersky Lab researchers said it was clear from lulls in the campaign that someone or something inside Google detected and removed many of the malicious ads distributing the Svpeng installation files. But even after old ones were expelled, new ones managed to take their place.
“The high rates and abrupt changes in the number of detections are easy to explain: Google has been quick to block the ads that the trojan uses for propagation,” the researchers wrote. “However, this is a reactive rather than proactive approach—the malicious ads were blocked after the trojan was already on thousands of Android devices. It is also worth noting that there were multiple occasions in the past two months when these ads found their way on to AdSense; similar attacks have been occurring up to the present time, with the most recent attack registered on 19 October 2016.”
Monday’s report is yet another reminder why it’s generally a good idea not to change default Android settings preventing the installation of apps not carried in the official Google Play app bazaar. It also reaffirms the importance of remaining highly skeptical of webpages encouraging users to install files. Google deserves credit for quickly removing malicious ads and creating safety nets such as Verify Apps and a default prohibition on installing third-party apps, but as the Kaspersky Lab researchers point out, these approaches reactively treat the symptoms rather than curing the underlying disease.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.