Websites offering free keygens for various enterprise software applications are helping crooks spread the Gatak malware, which opens backdoors on infected computers and facilitates attacks on a company’s internal network, or the theft of sensitive information.
Gatak is a backdoor trojan that first appeared in 2012. Another name for this threat is Stegoloader, and its main distinctive feature is its ability to communicate with its C&C servers via steganography.
Gatak relies on steganography to stain hidden
Steganography is the technique of hiding data in plain sight. In the world of cyber-security, steganography is the practice of hiding malicious code, commands, or malware configuration data inside PNG or JPG images.
The malware, in this case Gatak, connects to its online C&C server and requests new commands. Instead of receiving an HTTP network requests, for which all security software knows to be on the lookout, the data is sent as an innocuous image, which looks like regular web traffic.
The malware reads the image’s hidden data and executes the command, all while the local antivirus thinks the user has downloaded an image off the Internet.
Keygens for enterprise software spreading Gatak
Security firm Symantec says it uncovered a malware distribution campaign that leverages a website offering free keygens for various applications such as:
- SketchList3D – woodworking design software
- Native Instruments Drumlab – sound engineering software
- BobCAD-CAM – metalworking/manufacturing software
- BarTender Enterprise Automation – label and barcode creation software
- HDClone – hard disk cloning utility
- Siemens SIMATIC STEP 7 – industrial automation software
- CadSoft Eagle Professional – printed circuit board design software
- PremiumSoft Navicat Premium – database administration software
- Originlab Originpro – data analysis and graphing software
- Manctl Skanect – 3D scanning software
- Symantec System Recovery – backup and data recovery software
All of the above are specialized apps, deployed in enterprise environments. The group behind this campaign is specifically targeting users that use these applications at work, but without valid licenses, in the hopes of infecting valuable targets they could hack, steal data from, and possibly sell it on the underground.
Keygens don’t work, they just infect users with Gatak
The keygens distributed via this website aren’t even fully-working tools. They just produce a random string of characters, but their purpose is to trick the user into executing the keygen binary just once, enough to infect the victim.
The hackers are picky about the companies they target because the security firm has seen second-stage attacks on only 62% of all infected computers.
Attackers use Gatak to gather basic information about targets, on which, if they deem valuable, deploy other malware at later stages. In some cases, the hackers also resort to lateral movement on the victim’s network, with the attackers manually logging into the compromised PC.
Attacks aren’t sophisticated, and the hackers only take advantage of weak passwords inside the local network. Symantec says it didn’t detect any zero-days or automated hacking tools employed when hackers have attempted to infect other devices on the local network.
Telemetry data shows that 62% of all Gatak infections have been found on computers on enterprise networks.
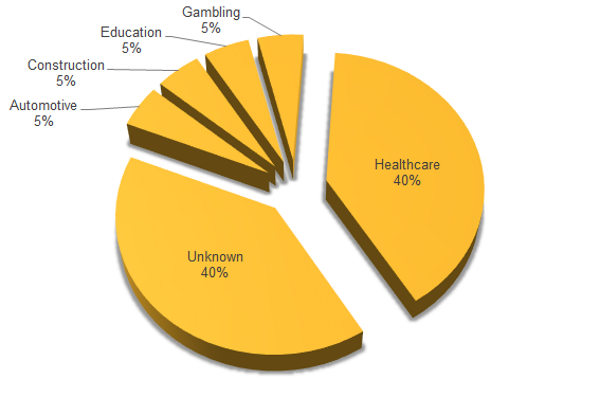
Most of these attacks have targeted the healthcare sector, but it doesn’t appear that hackers specifically targeted this industry vertical, as other companies in other verticals were also hit.
Attackers might have opted to focus more on healthcare institutions because these organizations usually store more in-depth user data they can steal, compared to the automotive industry, gambling, education, construction, or others.
“In some cases, the attackers have infected computers with other malware, including various ransomware variants and the Shylock financial Trojan,” Symantec notes in a report. “They may be used by the group when they believe their attack has been uncovered, in order to throw investigators off the scent.”

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.












