They promised they’d fix the issues and they didn’t, hacker says, so this latest breach shows better security is needed.
India is making the security headlines once again, this time after hackers managed to break into some of the high commission websites in the country and access login information of hundreds of users.
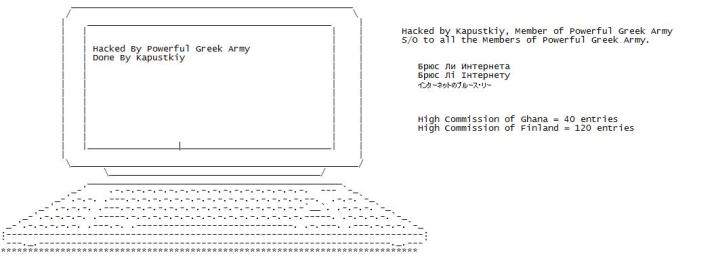
Kapustkiy, who describes himself as a security pentester and who is now a member of the Powerful Greek Army, accessed the database of two different high commission websites in India using an SQL injection that eventually exposed credentials of nearly 200 accounts, as he told us.
The High Commission of Ghana and the High Commission of Finland, both from India, were breached a few hours ago by Kapustkiy, who also decided to leak part of the database in order to give IT admins the time they need to patch the vulnerabilities.
Authorities ignoring security reports
Oddly enough, Kapustkiy says that he decided to breach Indian websites after local authorities failed to boost security and address the vulnerabilities that he previously discovered and which he used to access credentials of thousands of users.
“I had spoken with Yatin Patel (he runs all those sites) and he promised me a while ago that he would take a seriously look to it,” he told us earlier today. “I kept sending him emails but I did not get anything back from them because they claimed that they have fixed everything which is not true.”
What’s even more awkward is that Indian authorities publicly acknowledged vulnerabilities discovered by Kapustkiy and issued a thank you statement for the security pentester to show their appreciation for helping them address flaws that could expose users.
“Thank you for your advice,” Sanjay Kumar Verma, Joint Secretary, eGovernance and Information Technology, said recently. “We are fixing codes one by one. Your help in probing websites of various Indian embassies is a great help.”
Indian security engineers are more likely to look into this latest breach now that it went public, but in the future, it might be a good idea to actually fix them before user information is exposed.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











