Security experts from CloudFlare observed a new botnet that emerged in the wild and it could be dangerous as its predecessor Mirai.
Which is the most dreaded botnet in the current threat landscape? The Mirai botnet of course, it was used by threat actors in the wild to power massive DDoS attack, such as the one that hit the Dyn DNS service.
Now, security experts observed a new botnet is emerging in the wild and it could be dangerous as its predecessor Mirai.
The botnet was first spotted on November 23 by researchers at the content delivery network CloudFlare.
The DDoS attacks lasted 8.5 hours, attackers launched the offensive for six days at roughly the same time. The attacks were peaking at 400Gbps and hitting 320Gbps for hours on end.
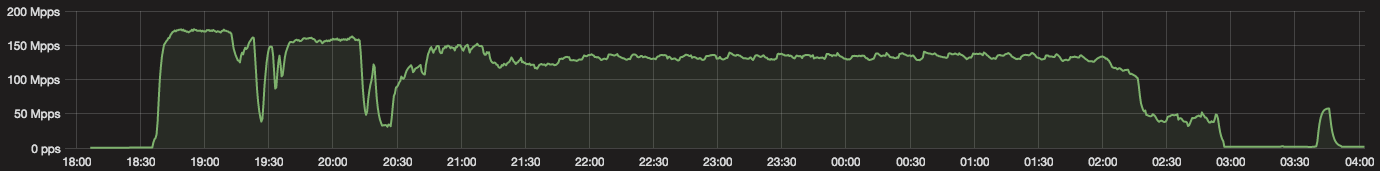
“On November 23, the day before US Thanksgiving, our systems detected and mitigated an attack that peaked at 172Mpps and 400Gbps.” states the report published CloudFlare. “The attack started at 1830 UTC and lasted non-stop for almost exactly 8.5 hours stopping at 0300 UTC. It felt as if an attacker ‘worked’ a day and then went home.”
The new string of cyber attacks are not powerful such as the ones launched through the Mirai malware, but anyway, they reached a significant volume.
Researchers discovered that the attacks are not powered from the Mirai botnet because they are launched from a differed software and are very large Layer3 and Layer4 DDoS attacks.
The researchers observed that the attacks were concentrated in a small number of locations mostly on the US west coast.
CloudFlare did not disclose further details of the DDoS attacks, it is not clear if the botnet is composed of IoT devices such as Mirai.
The new botnet will likely continue to grow and most experts fear it could be combined with other malicious infrastructure powering unprecedented DDoS attacks.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











