A bot farm involving hundreds of servers and over 570,000 different IP addresses has caused losses for online video advertisers ranging from $3 to $5 million per day.
This bot farm, nicknamed Methbot, dates back to September 2015, when US security firm White Ops had first detected signs of automated traffic coming from the crooks’ infrastructure.
The volume of this automated traffic sky-rocketed in October 2016, which led security researchers to start an investigation into its source.
Biggest ad fraud operation discovered to date
What White Ops discovered was a massive cybercrime operation that used 571,904 dedicated IPs, many falsely registered as US ISPs, and deployed between 800 and 1,200 dedicated servers in data centers in the Netherlands and the US.
The purpose of these data centers was to host lightweight JavaScript-based browsers that would carry out fictitious clicks, logins, and ad views for video advertisements shown on legitimate or spoofed sites.
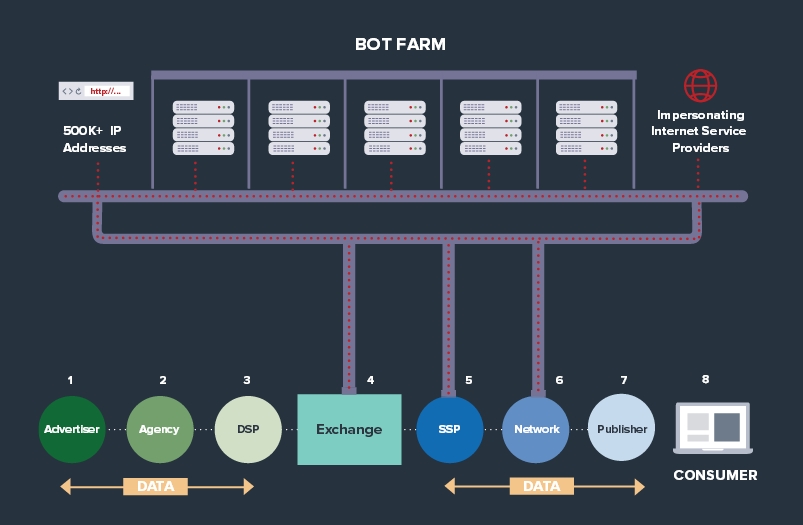
The Methbot crew, named so because of the many “meth” references in the infrastructure’s source code, earned money by posing as operators of high-profile websites and offering ad spots, which advertisers rented out.
The crooks then unleashed their bots on the rented ads, generating fake views by loading the page inside their Node.js-based browsers, viewing the ad, and sometimes clicking on it.
By switching their geo-location data and the source IP (they had 571,904 available), the crooks extracted click-per-impression fees from advertisers.
According to statistics gathered by White Ops, researcher believe that Methobot generated between 200 million to 300 million fraudulent video ad impressions per day.
White Ops: Methbot operators are Russian
According to a 30-page report on Methbot operations released today by White Ops, the group, suspected of being located in Russia, targeted the most expensive ad slots and high profile sites such as ESPN, Fortune, Huffington Post, Economist, CBS, Fox News, and Fortune. White Ops says the crooks spoofed over 250,000 URLs on over 6,000 domains.
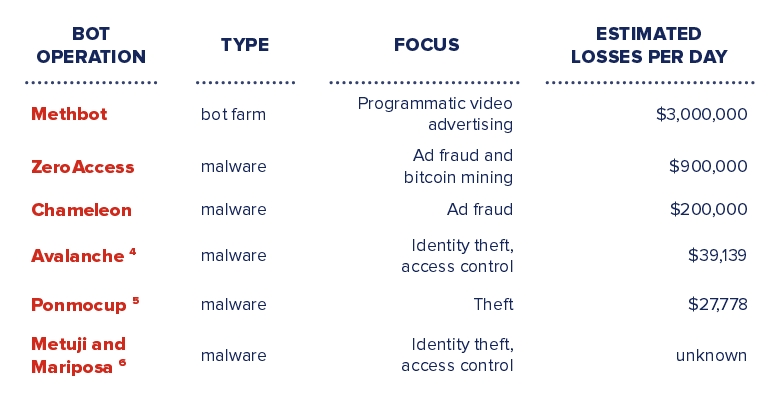
Compared to similar ad and click-fraud operations, Methbot is unique because it relied on data center servers, instead of botnets of computers and smartphones infected with malware, such as ZeroAccess, Chameleon, Ponmocup, Million-Machine, and HummingBad.
In fact, this was an advantage, because the Methbot crew earned from 3 to 5 times more from their operation, compared to a classic malware botnet system.
“The current complexity, interconnectivity, and resulting anonymity of the advertising ecosystem enabled the Methbot operators to exploit the entire marketplace,” researchers noted. “An impression may pass through many hands before it lands on a page and the ad is
served.
“Tracing that complete path back through the various marketplaces proves difficult due to walled gardens, reselling, competing interests, and limitations on human capital to devote to this initiative,” researchers added. “Close relationships between publishers and their advertisers may help circumvent much of this obfuscation and increase transparency, which will make it more difficult for even
advanced operations like Methbot to take advantage of the system.”

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











