An unknown hacker is accessing public and unsecured Apache Cassandra databases and adding an extra table through which it warns server owners that their DB was left exposed to online attacks.
The first cases of Cassandra databases with this extra table were spotted by a Twitter user that goes by the nickname of DunningKrugerEffect.
The name of this table is “your_db_is_not_secure,” and the table doesn’t hold any type of information inside.
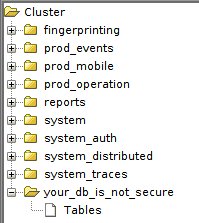

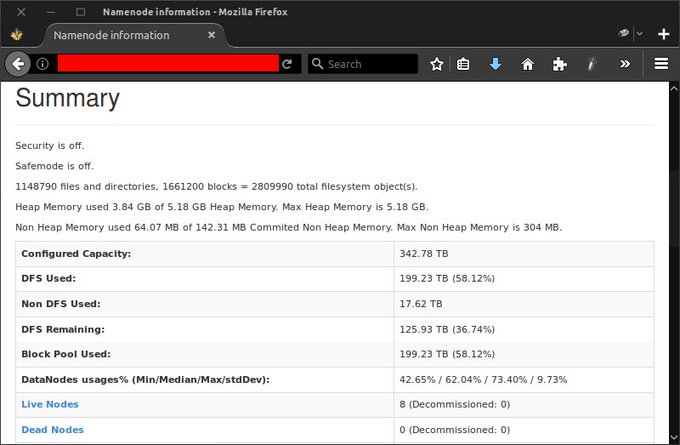
The purpose of this table is to warn Cassandra owners that their database can be very easily held for ransom in the upcoming few days if left online unprotected. According to Shodan, there are currently over 2,600 Cassandra database instances left accessible online.
Cassandra the next target?
Since the start of the year, multiple criminal groups have been hijacking database servers left unprotected online, wiping data and requesting a ransom payment.
First attacks hit MongoDB servers and were quickly followed by attacks against ElasticSearch clusters, Hadoop servers and CouchDB databases.
All previous attacks have been tracked by Victor Gevers and other members of the GDI.foundation, who created spreadsheets that keep track of ongoing attacks.
One such spreadsheet is available for Cassandra attacks. These are the latest statistics regarding database ransom attacks:
- MongoDB – 40,291 servers
- ElasticSearch – 5,044 servers
- Apache Hadoop – 186 servers
- Apache CouchDB – 452 servers
- Apache Cassandra – 49 servers
Currently, multiple members of the GDI.foundation “have been investigating these cases deploying honeypots and getting intel on the attacks,” Gevers tells Bleeping Computer.
The GDI.foundation has also been working with local CERT teams and attempting to notify database owners before attackers hijack their data. Despite this, very few server owners heeded their warnings, with many servers still remaining unsecured.

If you’re wondering what other database servers attackers could hit, there are Neo4J, Riak, or Redis systems that have not yet been targeted by these types of ransom attempts.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











