LeakedSource garnered criticism for actively cracking the passwords it sold.
LeakedSource, a legally and ethically questionable website that sold access to a database of more than 3.1 billion compromised account passwords, has disappeared amid an unconfirmed report that its operator was raided by law enforcement officers.
“Leakedsource is down forever and won’t be coming back,” a person using the handle LTD wrote Thursday in an online forum. “Owner raided early this morning. Wasn’t arrested, but all [solid state drives] got taken, and Leakedsource servers got subpoenaed and placed under federal investigation. If somehow he recovers from this and launches LS again, then I’ll be wrong. But I am not wrong.”
Attempts to reach LeakedSource operators for comment weren’t successful.
From the beginning of LeakedSource’s 15-month history, ethical and legal questions dogged the service. Not only did it provide billions of passwords for compromised accounts to anyone paying a subscription fee, site operators actively converted cryptographically protected data into the plaintext passwords needed for people to gain unauthorized access to those accounts. That left the site open to charges that it made breaches on third-party sites worse by making the compromised data available to large numbers of people. Those people, in turn, could use the data to take over the affected accounts or see if the affected holders used the same password on other services.
“Leaked Source was always going to inevitably face serious consequences by providing the passwords of data breach victims to anyone willing to pay for them,” researcher Troy Hunt, who operates the free breach-notification service Have I Been Pwned, told Ars. “I was shocked when someone bought access to their service, then sent me my own password from a data breach.”
Have I Been Pwned, by contrast, never makes the password data available in any form, a measure that helps contain the damage when accounts are compromised. Hunt’s service also doesn’t crack password hashes.
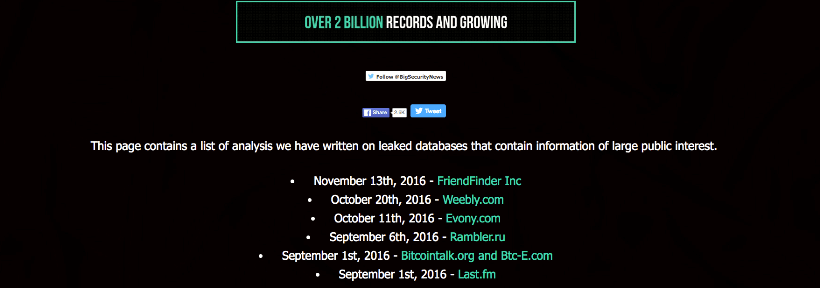
Despite the unsavoriness, LeakedSource became a go-to resource for journalists, researchers, and hackers who wanted to stay abreast of the latest website breaches. The hacks it brought to light included those hitting the AdultFriendFinder network with more than 412 million affected accounts, gaming company Evony with more than 33 million compromised users, and Russian Internet portal Rambler.ru with 98 million compromised users. LeakedSource often provided detailed breach news days or weeks before it was available anywhere else.
It’s not clear where LeakedSource hard drives and servers were located, or assuming the report of a raid is true, what law enforcement agency was involved. The above-linked forum thread indicates that multiple parties obtained copies of the LeakedSource database. It wouldn’t be surprising if it was republished on a new site.
Source:https://arstechnica.com/security/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.