Programming blunders allow miscreants to snatch home gateways’ admin passwords.
Researchers are warning of a serious security hole that can be exploited to hijack potentially hundreds of thousands of Netgear routers.
The programming blunder allows an attacker with access to the router to harvest the administrator access password. A victim could visit a malicious webpage that uses JavaScript to exploit the vulnerability in the router firmware to take over the boxes, knock them offline, change their DNS settings to redirect browsers to malware-injecting websites, and so on. Malware already on the local network can also target the security flaw.
The bug can even be exploited from across the internet if the device is set up to expose its admin interface to the whole web, but this is not a default setting.
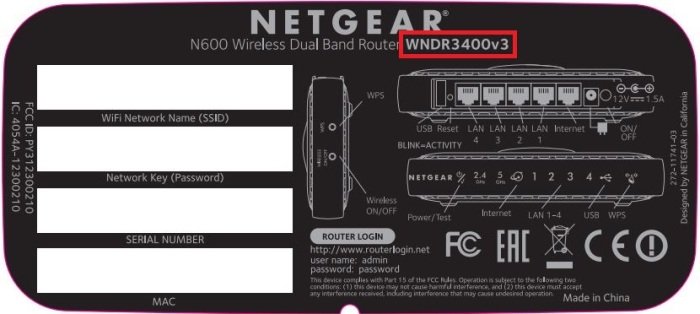
This particular security hole is believed to be present in 31 different Netgear models. Owners of at-risk kit are advised to check and update their firmware.
The flaws, designated CVE-2017-5521 and TWSL2017-003, were discovered by researcher Simon Kenin of Trustwave, who found that by triggering an error message, the router can be tricked into handing over a numerical code that can then be used with the password recovery tool to retrieve the router’s administrator credentials.
Further research led Kenin to discover that in many cases, the numerical code is not even necessary, and that random strings sent directly to the password recovery script would still cause the login information to be displayed.
In short, anyone who can pull up the router administrator screen, be it over the web or local Wi-Fi network, can obtain the admin password and gain complete control over the router itself.
“We have found more than ten thousand vulnerable devices that are remotely accessible,” said Kenin. “The real number of affected devices is probably in the hundreds of thousands, if not over a million.”
Netgear has released a fix for the update, though Kenin says that getting the network hardware giant to pay attention to the report was a nine-month ordeal that culminated in Netgear’s commitment to overhaul its handling of bug reports and work more closely with the research community.
The vulnerability is one of several high-profile flaws to be found in Netgear’s routers in recent months. On two occasions in December, researchers disclosed security flaws in the router that, like Kenin’s bugs, could be exploited remotely to take control over the device.
Mike Ahmadi, global director of critical systems security with Synopsys, says the cause of the problem is not unique to Netgear, but rather something every network hardware builder has to deal with.
“Vendors typically build such devices for the stated functionality, which is to route traffic and block unwanted traffic, when used as intended,” Amadi said.
“What many vendors fail to do, however, is adequately assess the inherent security of the devices they sell, thereby flooding the market with vulnerable devices. Some vendors have taken it upon themselves to address the inherent vulnerabilities, but the end user is often left guessing which devices are adequately tested, since there is currently no regulatory requirement to test to a given level of rigor.
Source:https://www.theregister.co.uk/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.