The Australian Nuclear Science and Technology Organization was hacked last Friday, but members were only just informed.
The Australian Nuclear Science and Technology Organization (ANSTO) was hit by hackers who stole scientists’ usernames and passwords.
According to The Register, hackers hit systems hosting the web portal that is used by researchers from ANSTO, as well as third parties and got away with usernames, email addresses, and some scrambled passwords.
An email sent to users of the Australian Synchrotron User Portal indicates the breach took place on January 27, but there is no mention of how the hackers got it. Users are advised to change their passwords.
The email further states that immediate action was taken to address the vulnerability and there’s a security review of the Australian Synchrotron User Portal underway, with no mention as to why it took nearly a week to inform everyone of the situation. Given how often people reuse their emails and passwords on other platforms, the delay put people’s data further at risk.
Additional data
It is unclear whether all the data from people’s accounts was taken or just the aforementioned emails and passwords. That’s because the portal requires people to fill out full names, academic qualifications, the organization they work for, complete with department and position. Additional fields can be filled in with home address, phone number, citizenship, and gender, but these are not mandatory.
The ANSTO claims that passwords were encrypted, but they do not mention what method was used. Given the nature of the organization, we hope that a proper algorithm was used that can actually hold up against hackers. We just hope that the adviser for users to change passwords was just a precautionary measure and not an indication that some weak algorithm was used for encryption.
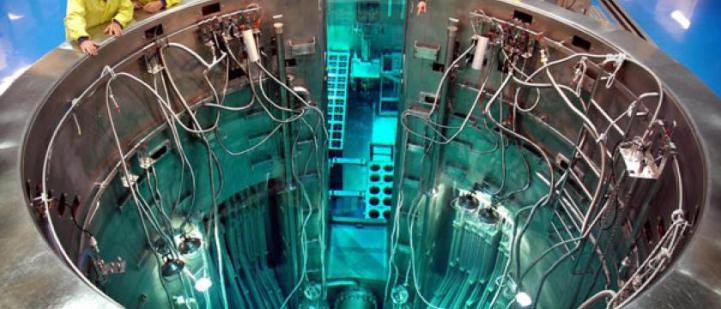
It should be mentioned that the database is isolated from the nuclear reactor that’s also on the campus where ANSTO is located.
Source:https://news.softpedia.com

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.