A ransomware infection that took root on late Tuesday night, January 31, affected several services provided by the local Licking County (Ohio) government infrastructure.
The Linking County Commissioner’s Office acknowledged the incident in a series of Facebook posts
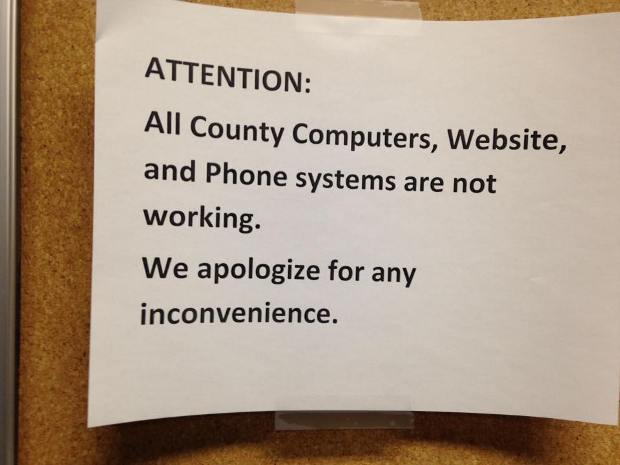
According to officials, all government offices have been affected, some indirectly, after IT staff turned off the phones and computer system to deal with the infection’s damage.
County officials said all offices would be open as usual, but employees will most likely operate using pen and paper for the rest of the week.
Local news outlet Newark Advocate reports that some government workers that work in data entry and can’t use their computers have been sent home, while others have been assigned field duty.
911 emergency services also affected
The computer network at the local 911 emergency services was also affected, but the phone systems were on a separate line and continued to work. The lack of access to the emergency system’s computer network has significantly reduced the efficiency of 911 operators.
Licking County officials declined to comment on the ransom demand’s size, or if they’ll pay. It is unknown if the County’s IT staff is restoring computers from backups, or just wiping and reinstalling systems. The point and method of the initial infections is also currently unknown.
Law enforcement and the FBI have been notified of the attack and are investigating.
In an unrelated incident, two days later, on Thursday, February 2, a spokesperson for the city of Troy, New York, admitted to a similar ransomware incident that has shut down the local government’s computer system.
Source:https://www.bleepingcomputer.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.