An ultranationalist developer from Serbia is behind a series of malware strains, including a new ransomware family named SerbRansom, discovered yesterday by security researcher MalwareHunter.
The ransomware itself is not a big threat at the moment, as it doesn’t appear to be part of a mass distribution campaign. Additionally, the quality of its source code is also inferior to most ransomware families we’ve seen in the past.
According to MalwareHunter, there have been no users who tried to identify ransomware infections via the ID-Ransomware service, which is somewhat of a good news. If anyone would be infected by this threat, they would see a window showing the following message:
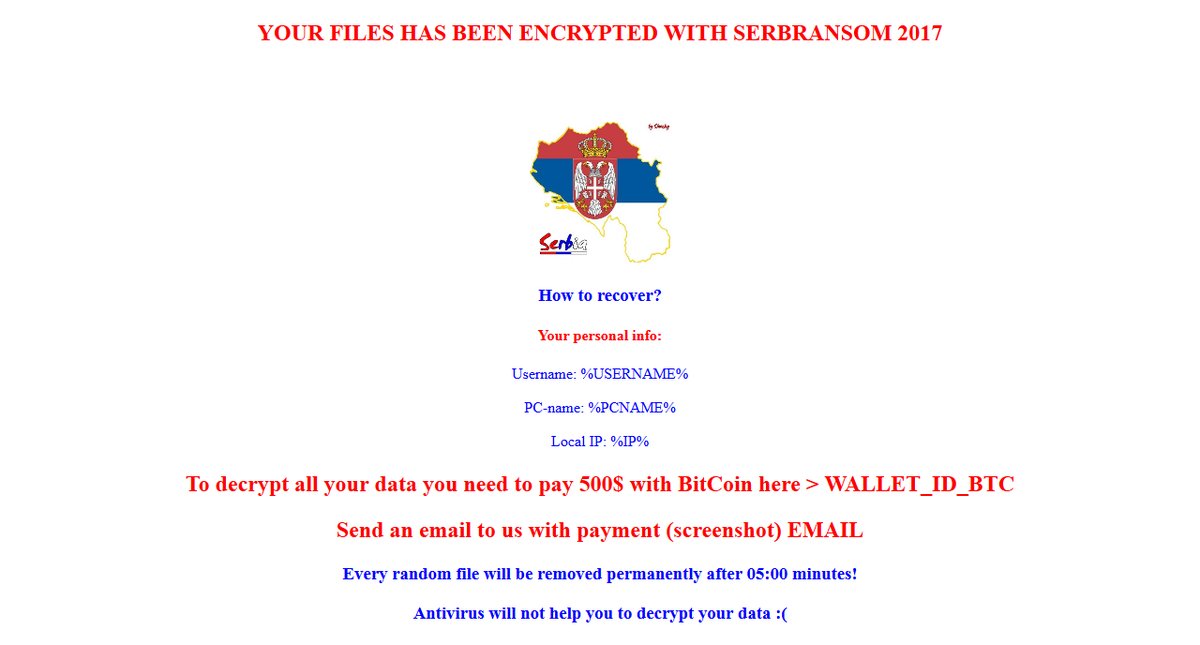
The ransom note includes an ominous message which states that every five minutes, SerbRansom will delete a random file. This claim is false, as there was no file deletion in any of our tests.
According to MalwareHunter and Bleeping Computer’s Lawrence Abrams, the ransomware overall is very basic and uses simple encryption.
SerbRansom created via a builder
MalwareHunter has also discovered SerbRansom’s builder, an application that allows its creator to generate custom SerbRansom versions.
As you can see from the image below, the builder lets the author customize:
- The file types to encrypt
- The encryption key
- The Bitcoin wallet ID showed in the ransom note
- The email account where victims can get in touch
- The extension added at the end of encrypted files
- The maximum size of files the ransomware should encrypt
- If to use a UAC bypass
- If to obfuscate the ransomware binary
- If to deploy anti-sandboxing techniques
- If to remove system restore points
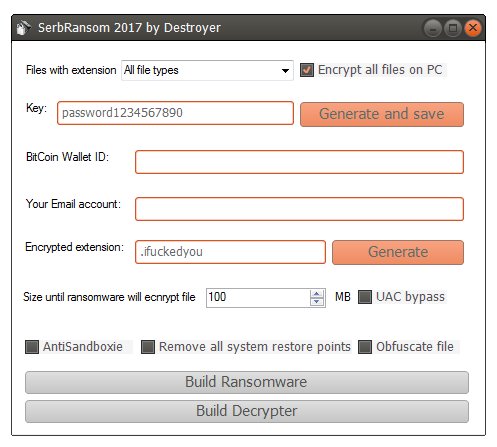
The SerbRansom builder can be used to create both the ransomware payload and the decrypter itself, the file crooks sent back to victims that paid.
Furthermore, the presence of a builder also means that the author of this tool might soon attempt to monetize it, as it allows non-technical users to create and deploy ransomware with a point-and-click experience.
SerbRansom’s author doesn’t like neighboring countries
On the background of the SerbRansom ransom note, the ransomware will play the audio of this YouTube video, which is a Serbian national song associated with the “Kosovo is Serbia” movement.
Clues left in the ransomware’s source code have tied this ransomware to a hacker known as R4z0rx0r, who on a forum profile, self-identifies as a Serbian male.
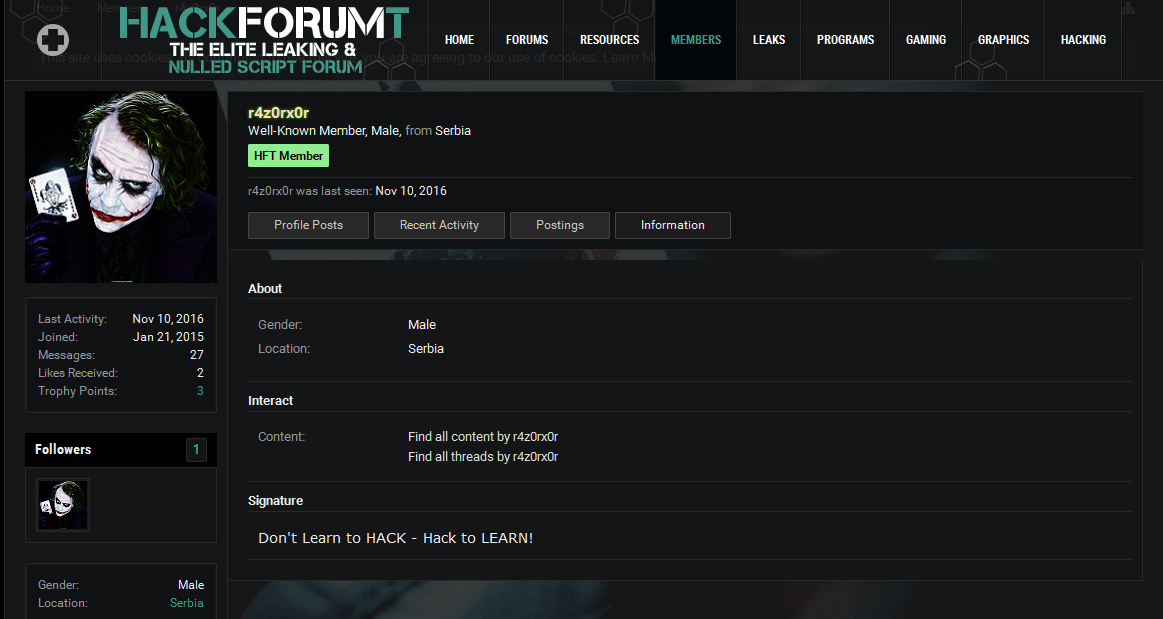
The HackForumT board is a place where users share nulled scripts, and sometimes cracked hacking tools.
From R4z0rx0r’s past forum posts, we can see how the hacker evolved. Past posts clearly identify his interested in all sorts of cracked hacking tools. For the past two years, he showed interested in DDoS tools, RATs, crypters, Google dorking tools, account cracking tools for adult websites, social media account stealers, and others.
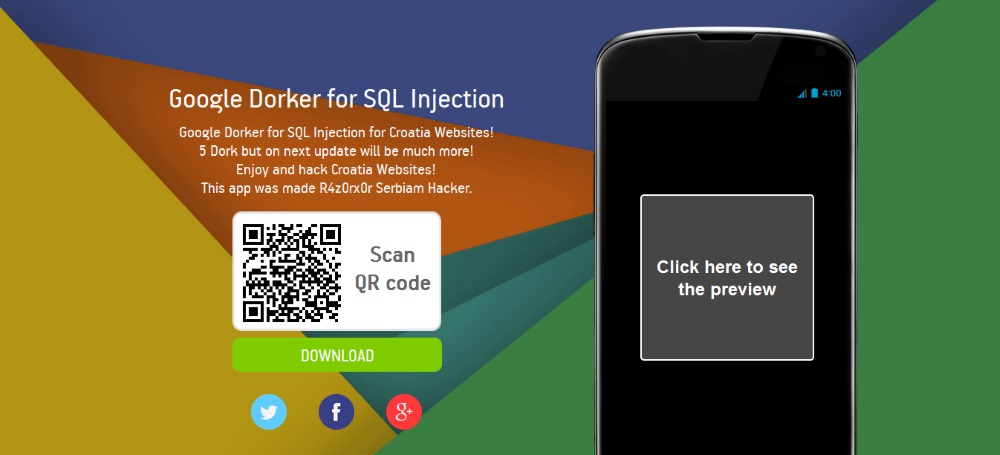
His name also appears on a website that offers a free Android app named “Google Dorker for SQL Injection,” which the hacker claims he specifically built for targeting Croatian websites, a country with which Serbia waged a war at the start of the 90s.
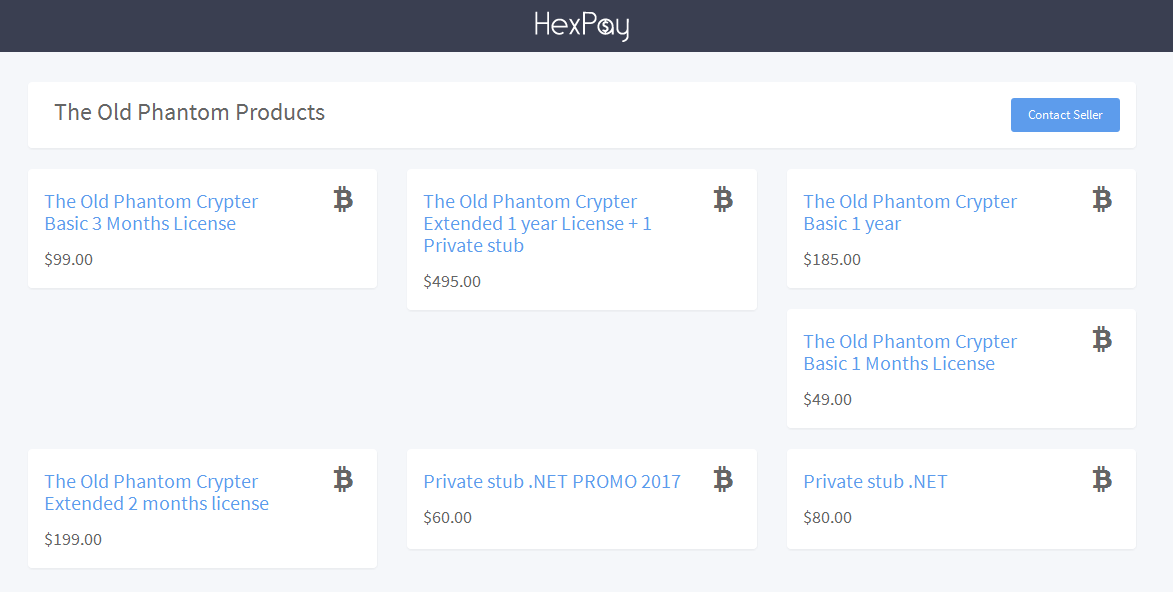
Besides the Android app, R4z0rx0r and another unknown developer are behind a new crypter that they’re peddling online for prices ranging from $49 to $495.
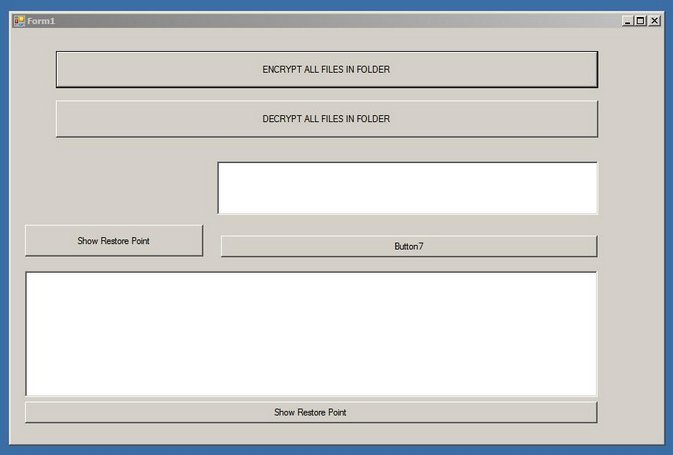
Furthermore, MalwareHunter also discovered another tool tied to R4z0rx0r, which appears to be a custom-built utility which the hacker might be using to encrypt data on computers he gains access to by brute-forcing RDP ports. This is only a theory, though.
Files encrypted with this tool receive a new extension named “.razarac”, which is the Serbian word for “destroyer.”
Digging a little deeper, MalwareHunter also identified what could be the hacker’s real-life identity, but we chose not to publis this information, since we couldn’t verify that the person we identified was indeed R4z0rx0r.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











