Delivered by “secure” Word doc, pure PowerShell malware fetches commands from DNS TXT records.
Researchers at Cisco’s Talos threat research group are publishing research today on a targeted attack delivered by a malicious Microsoft Word document that goes to great lengths to conceal its operations. Based entirely on Windows PowerShell scripts, the remote access tool communicates with the attacker behind it through a service that is nearly never blocked: the Domain Name Service.
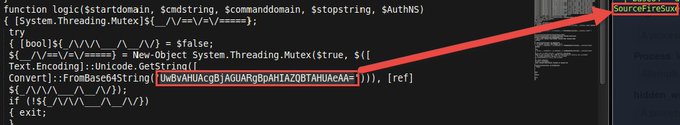
The malware was first discovered by a security researcher (@simpo13) who alerted Talos because of one peculiar feature of the code that he discovered: it called out Cisco’s SourceFire security appliances in particular with the encoded text, “SourceFireSux.”
Delivered as an e-mail attachment, the malicious Word document was crafted “to appear as if it were associated with a secure e-mail service that is secured by McAfee,” wrote Talos researchers Edmund Brumaghin and Colin Grady in a blog post to be published later today.
Once opened, the document launches a Visual Basic for Applications macro (which was previously spotted and posted to PasteBin, apparently by Microsoft Threat Intelligence Center General Manager John Lambert) to launch PowerShell commands to install the backdoor onto the system. “The hash listed in the Pastebin led us to a malicious Word document that had also been uploaded to a public sandbox,” the Talos researchers wrote. “The Word document initiated the same multiple-stage infection process as the file from the Hybrid Analysis report we previously discovered, and allowed us to reconstruct a more complete infection process.”
The VBA script unpacks a compressed and obfuscated second stage of PowerShell, which determines whether the user who let loose the malware has administrative access and what version of PowerShell is installed on the system. It then makes changes to the Windows Registry and installs a third stage—a PowerShell script that acts as a discreet, simple backdoor. If the user does have administrative access, the installer PowerShell then adds the backdoor to the Windows Management Instrumentation (WMI) database—allowing it to stay persistent on the system after reboot.
The backdoor periodically makes DNS requests to one of a series of domains hard-coded into the script. As part of those requests, it retrieves TXT records from the domain, which contain further PowerShell commands—commands that are executed but never written to the local system. This “fourth stage” script is the actual remote control tool used by the attacker. “Stage 4 is responsible for querying the C2 servers via DNS TXT message requests to ask what commands to execute,” Edmund Brumaghin told Ars via e-mail. “If a command is received, it is then executed and the output or results of the command are communicated back to the C2 server. This basically gives the attacker the ability to execute any Windows or application commands available on the infected host.”
Just what sort of malicious commands the attacker was using this DNS backdoor to execute isn’t known. “We were unable to get the C2 infrastructure to issue us commands during our testing,” Brumaghin said. “Given the targeted nature of this attack, it is likely that the attackers would only issue active C2 commands to their intended target.”
The irony of this particular attack calling out SourceFire is that Cisco has just relaunched Umbrella—a service it acquired with OpenDNS—a product that is intended to shield from DNS exploits precisely like this.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











