WhatsApp and Telegram have patched their respective web clients against a common security flaw discovered by researchers from Israeli firm Check Point, a security issue that would have allowed an attacker to take over user accounts and spy on conversations or steal user account data.
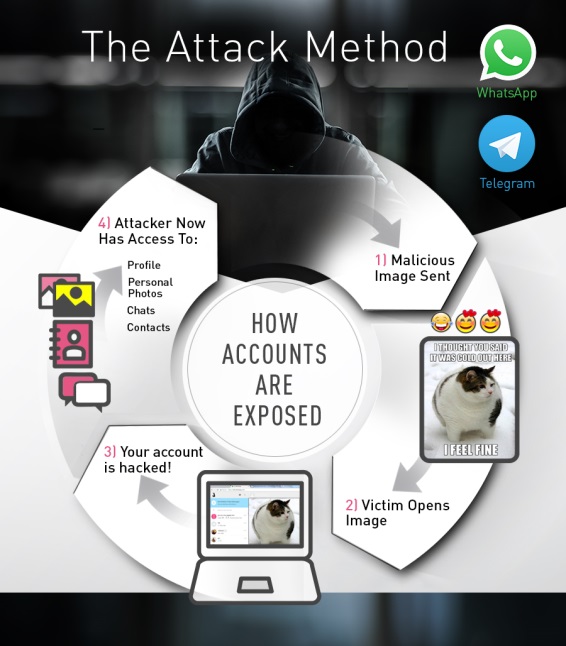
According to researchers, the entry point was an attacker’s ability to upload and send malicious code hidden inside HTML files.
Both WhatsApp and Telegram would show a preview image for these links, making users believe they were accessing a video or image.
Exploit granted attackers access to browser’s localStorage
In reality, when users clicked the links, malicious JavaScript code contained in the HTML files would execute and steal data from the user’s browser localStorage.
In layman’s terms, localStorage is a term that describes a local container in the user’s browser where data about a web application is stored.
The type of data usually found in WhatsApp and Telegram localStorage containers includes the user’s friends list, chat history, and past file transfers.
Flaw could be used to transcend attacks on mobiles
Depending on the attacker’s skill level, he could extract this data from localStorage, but also use the malicious JavaScript code to send new commands to the WhatsApp and Telegram web clients.
For example, JavaScript code could replace localStorage data and include new links or messages in a conversation from a trusted source that users might click or read and take at face value.
Furthermore, these messages are also automatically synced to the victim’s phone, meaning a compromise of the web client could be used to intermediate attacks on the user’s phone.
Check Point informed both WhatsApp and Telegram of this flaw last week. Both companies patched the issue. The patch was a server-side fix, meaning users don’t have to do anything, their browser already having loaded the latest version of the web clients.
The fix was an update to the way both services scan transfer files. Both WhatsApp and Telegram now validate the content of file transfers before the encryption process kicks in, not after, as they did until now.
Source:https://www.bleepingcomputer.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











