After last month security researchers discovered the first-ever Word document spreading macro malware on macOS, last week, researchers from Fortinet spotted a Word document that contained macro scripts that distributed both Windows and macOS malware at the same time, depending on the OS it managed to infect.
Malicious Office files with attached macro scripts that download malware are usually referred in the infosec industry as “macro malware.”
On Windows, macro malware has been around since the 90s. Even if Microsoft offered an Office version for Mac OS X (now macOS), weaponized Office files never contained macro scripts that could run on a Mac.
Macro malware rears its ugly head on macOS
The first fully working macOS macro malware was spotted at the start of February by Symantec and Synack researchers, who found a malicious Word document that used Python code embedded in the macro script to download a malicious payload from a remote server. Because the C&C server was down, researchers couldn’t tell what the payload was used for.
Last week, Fortinet researchers discovered a similar Word file, also containing Python code embedded in its macro script.
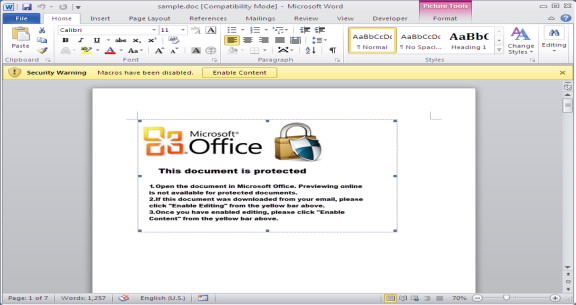
The difference was that at the start of its malicious routine, the macro would check what OS the user was using, and delivered two different versions of the malicious Python code.
Regardless of the OS, both scripts behaved relatively the same, by using modules from the Meterpreter framework to contact a remote C&C server and request a final payload.
As in the case of the February macOS macro malware incident, the C&C server was down, and researchers couldn’t tell what exactly the malware did, on Windows or macOS.
This is the first documented case where crooks merged attack code for both operating systems inside the same macro script.
This incident doesn’t mean anything in particular for Windows users, who have become accustomed to macro-laced Word documents. On the other hand, macOS users should take note and be aware of this new attack vector.
Source:https://www.bleepingcomputer.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











