The author of the Nuclear Bot banking trojan has leaked the source code of his own malware in a desperate attempt to regain trust and credibility in underground cybercrime forums.
Nuclear Bot, also known as NukeBot and more recently as Micro Banking Trojan and TinyNuke, is a new banking trojan that appeared on the malware scene in December 2016, when its author, a malware coder known as Gosya, started advertising it on an underground malware forum.
According to Gosya’s ad, this new banking trojan was available for rent and included several features, such as:
- Formgrabber and Web-Injection modules (Firefox, Chrome, IE, and Opera)
- A SOCKS proxy module
- Remote EXE file launcher module
- Hidden VNC module that worked on Windows versions between XP and 10
- Rootkit for 32-bit and 64-bit architectures
- UAC bypass
- Windows Firewall bypass
- IBM Trusteer firewall bypass
- Bot-killer – a mini anti-virus meant to remove all competing malware from the infected machine
Subsequent analysis from both Arbor Networks and Sixgill confirmed the trojan’s deadly features. In spite of these favorable reports, Gosya’s Nuclear Bot saw little adoption among cybercrime gangs, as the malware’s author miserably failed to gain their trust.
Gosya broke many unwritten rules
The reason for his poor success, according to IBM X-Force, is that Gosya broke many unwritten rules of the cybercrime community he was trying to sell to, which initially was a private, Russian-speaking forum.
The rules on these forums are extremely strict, as hackers and malware authors do their best to root out malware researchers and law enforcement agents.
As such, every new member must be introduced by a known forum user. While in the beginning Gosya was presented to the community by another reputable hacker, IBM experts say he broke almost every rule after that.
As soon as he managed to get his hands on a forum profile, Gosya started to aggressively advertise his Nuclear Bot. While not a major mistake, Gosya continued to break unwritten rules by failing to provide a test version of his malware to both admins and potential buyers.
Without a test version to have his banking trojan evaluated, his reputation quickly went downhill, as most members labeled him a scammer, and questioned his trojan’s features.
Nuclear Bot’s marketing failed miserably
According to IBM, the biggest criticism came from the operators of the FlokiBot banking trojan, who smelled blood in the water and asked complicated questions, to which Gosya provided insufficient answers, raising even more suspicions among community members that he was the author of the malware he was selling. With his technical skills questioned, many potential buyers thought twice before buying his malware.
The fact that Nuclear Bot was available for $2,500 per month, twice the price of its nearest competitor, didn’t help either.
With no test version available for members, his reputation went downhill in a matter of weeks. Panicking, Gosya made his biggest mistake when he started selling Nuclear Bot on multiple forums, which is a big no-no in the malware scene.
Even worse, Gosya then switched nicknames and even rebranded Nuclear Bot as Micro Banking Trojan. This last act solidified his reputation as a “scammer” in the eyes of the entire underground hacking community, and he was eventually banned from multiple forums.
Nuclear Bot was a real, fully functional banking trojan
IBM notes with irony that despite being shunned by the cybercrime community, Nuclear Bot was actually a fully-working banking trojan that “does not fall short of other.”
The trojan didn’t fail technical tests, but in its marketing department, where the more experience FlokiBot gang gained a big piece of the market.
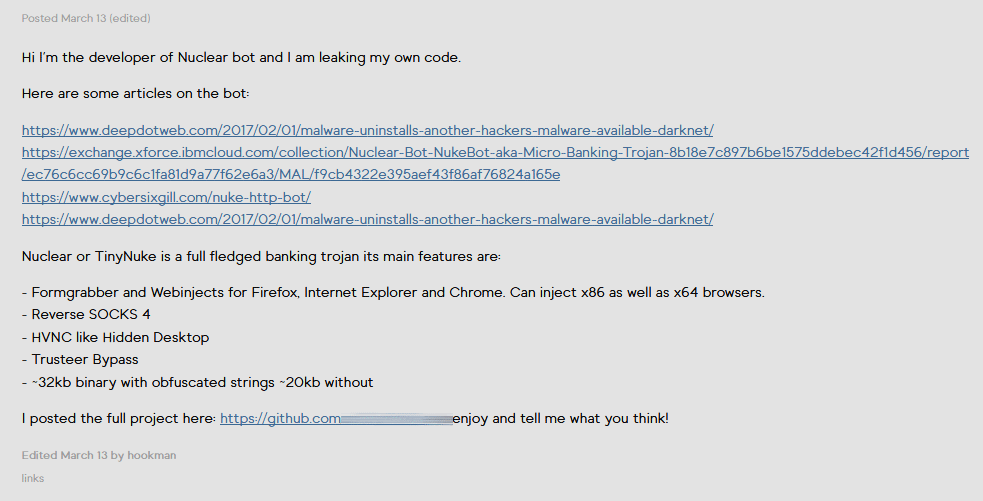
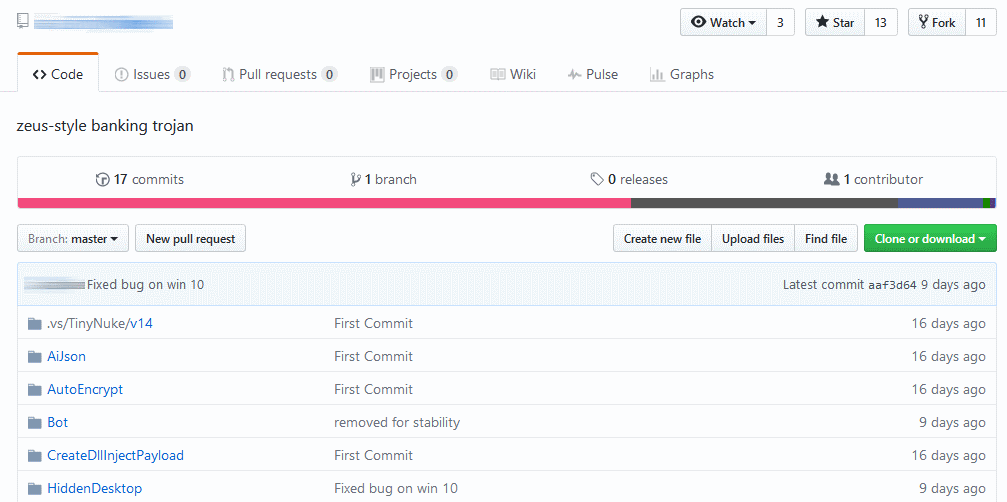
Nevertheless, in an attempt to rebuild his reputation, on March 13, Gosya went on several online forums and posted links to a GitHub repo where he leaked the Nuclear Bot source code, by this time rebranded as TinyNuke.
Despite being quite a potent banking trojan, IBM said it didn’t detect active campaigns distributing Nuclear Bot, but this is very likely to change.
“With yet another malware source code out in the open, the most likely scenario is that NukeBot code will be recompiled and used by botnet operators,” IBM’s Limor Kessem said. “Parts of it may be embedded into other malware codes, and we are likely to see actual NukeBot fraud attacks in the wild in the coming months.”
Kessem believes that by leaking Nuclear Bot’s source code, Gosya might have regained some of his credibility back, and might soon be allowed back on the same forums he is currently banned.
While Gosya might hope to make money from developing new Nuclear Bot modules, history tells us different.
In the past, whenever the source code of a malware family leaked online, it usually spelled the malware’s end. Nonetheless, Gosya might be happy just to get his reputation back.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











