A cyber-espionage group that first surfaced in 2009 is using a novel tactic into hacking its targets by first breaching one of its cloud service providers, and then reaching inside the company’s secure business network via the cloud service’s approved communications channels.
The tactics of this group are new and haven’t been seen before. Until now, cyber-espionage groups, regardless of affiliation, used cloud providers mainly to store malware or as relay points for stolen data.
This group’s decision to hack the cloud service providers comes as these services are becoming more ubiquitous in enterprise networks, and almost all companies use one or more cloud services to handle some type of activity, may it be human resource management, inventory activities, email, or file sharing and hosting.
Hackers use cloud services to hide malicious activity
This particular group of Chinese hackers is known in the infosec community under different names, such as APT10 (FireEye), Red Apollo (PwC), CVNX (BAE Systems), Stone Panda (CrowdStrike), POTASSIUM (Microsoft), and MenuPass (Trend Micro).
Until recently, its activity involved the classic method of using spear-phishing attacks aimed at individuals inside corporate or government networks.
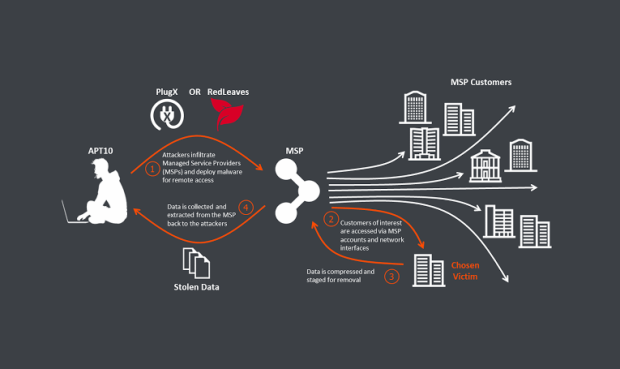
As of late 2016, BAE and PwC researchers both noted a change in the targeting of APT10. Instead of going after employees working in secure and hardened enterprise networks, where’s there’s a chance to get caught, attackers started targeting individuals at cloud service providers, which don’t always feature the same level of security protections.
Once APT10 operators get a foothold inside these companies, they take over their systems and use the access the cloud service has to the enterprise networks to infiltrate and hack the cloud provider’s clients.
All infiltration and exfiltration operations are handled via the cloud service’s regular communications channels, which are usually whitelisted inside the clients’ networks.
Hackers breached companies all over the globe
In a comprehensive report detailing all these activities released yesterday by BAE and PwC, researchers said APT10 managed to hack companies in the UK, US, India, Japan, France, Brazil, Canada, South Africa, Australia, Thailand, and South Korea.
The targeted companies were active in various sectors, revealing both the targeted nature of these attacks (against the cloud provider), but also an element of randomness (against its customers). Basically, attackers breached a cloud provider and then ransacked what they could from their biggest customers.
For their attacks, the group used PlugX, a backdoor trojan seemingly used by almost all Chinese espionage groups, but also a newly-created backdoor called RedLeaves, used only by APT10.
BAE and PwC didn’t reveal a list of hacked cloud service providers, but the report also includes IOCs, if sysadmins need to update their firewalls and security platforms.
Source:https://www.bleepingcomputer.com

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.