There’s a group of hackers who are hijacking unsecured home routers and using these devices to launch coordinated brute-force attacks on the administration panel of WordPress sites.
The purpose of these attacks is for the hackers to guess the password for the admin account and take over the attacked site.
The routers play a crucial role in this scenario, as it allows hackers to spread their brute-forcing attack over thousands of different IP addresses, avoiding firewalls and their blacklists.
Routers hijacked via port 7547
WordPress security firm WordFence, who uncovered these attacks, says the group behind this campaign is leveraging security flaws [1, 2] in the TR-069 router management protocol to take over devices. These flaw can be exploited by sending malicious requests to a router’s 7547 port.
Experts say the attackers are launching only a few password-guessing attempts from each router on purpose, to keep a low profile for their attacks.
The size of the botnet is unknown, but there could also be more than one botnet. WordFence says that 6.7% of all brute-force attacks on WordPress sites in March 2017 came from home routers with port 7547 left open on the Internet.
Attacks coming from the networks of 28 ISPs
The company has tracked down many of the biggest offenders to 28 ISPs around the world, 14 of which feature a massive amount of routers with their 7547 management port left open to external connections. A list of the offending ISPs is available here.
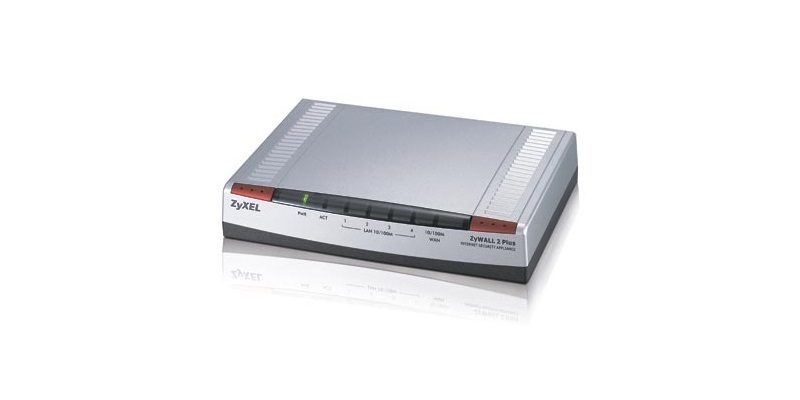
In many of these incidents, the attacks were tracked down to ZyXEL ZyWALL 2 routers. ZyXEL routers are well known for their TR-069 flaws.
At the end of last year, a hacker tried to hijack over one million routers from the networks of ISPs in Germany and the UK. Many of those routers were ZyXEL or rebranded ZyXEL routers. The hacker meant to add the routers to a Mirai botnet he was renting for DDoS attacks. UK police eventually apprehended a suspect in February.
ISPs could easily stop these attacks
For some time now, security experts have been recommending users to limit access to their router’s 7547 port. Taking into account that the vast majority of home users aren’t technically trained, such advice is useless 99.99% of the time, since most routers don’t allow this.
Better advice is provided by WordFence, who argues that “ISPs should filter out traffic on their network coming from the public internet that is targeting port 7547.”
“The only traffic that should be allowed is traffic from their own Auto Configuration Servers or ACS servers to and from customer equipment,” said Mark Maunder, WordFence CEO.
Routers are a weak spot in our home networks
This is not the first time crooks find innovative ways to use home routers. Last year, the operators of a malvertising campaign used JavaScript code hidden in malicious ads to hijack 166 home router models. After taking over these devices, crooks used them to redirect users to malicious sites or to replace ads on legitimate sites.
Last week, ESET discovered the Sathurbot botnet, created using PCs infected via torrent files, and also used to launch brute-force attacks on WordPress sites.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











