On Friday, April 7, the FBI arrested Zhengquan Zhang, a 31-year-old IT engineer, who now stands accused of installing malware on his employer’s servers to steal proprietary source.
Zhang started working for his former employer, KCG Holdings, Inc., in March 2010, first in its New York branch, and then its San Francisco offices. During his stint with the company, a Wall Street securities firm, Zhang worked as a DevOps engineer and was later promoted to a supervisor role, in charge of several other engineers.
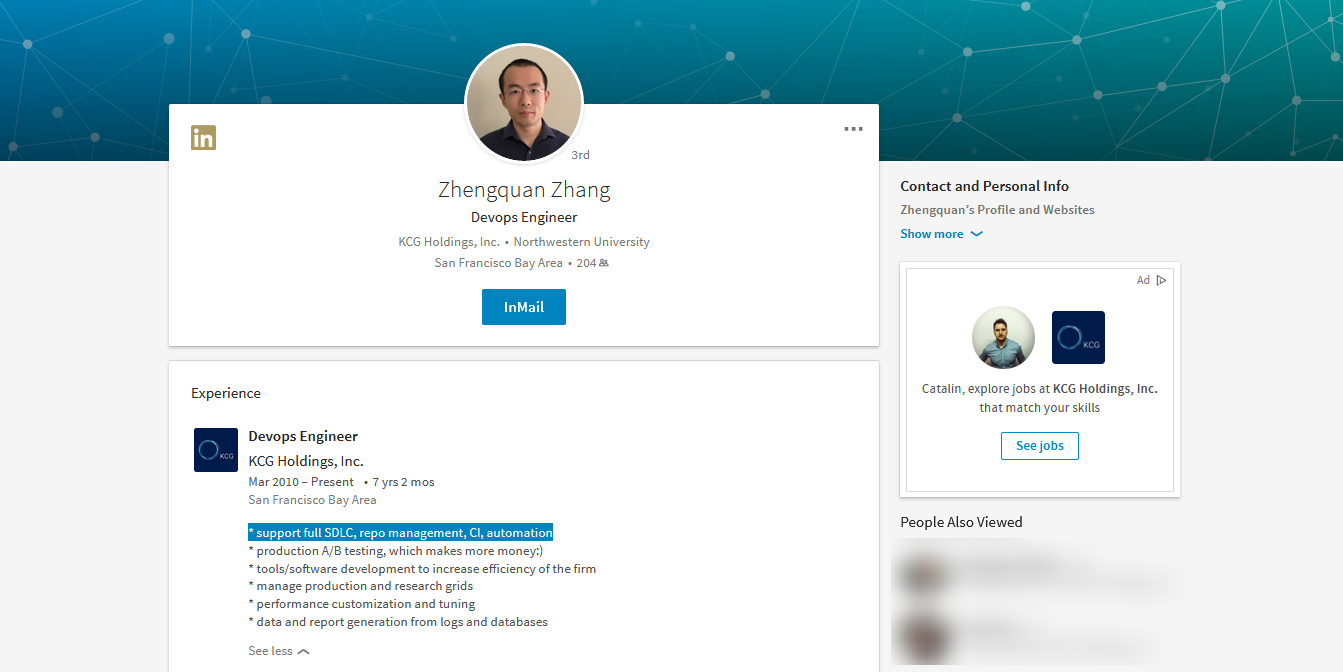
Among Zhang’s duties, according to his LinkedIn page and an FBI affidavit, the suspect was tasked with managing the source code of KCG’s trading platform and the trading algorithms the company used to automate some of its financial transactions.
Access to this repository was granted only to approved employees and based on encryption keys that decrypted the source code based on each employee’s access level.
Zhang’s hacking uncovered last month
On Saturday, March 25, a quantitive analyst working for KCG from home logged in remotely into his work computer.
Shortly after, the analyst was disconnected from his session, and on re-opening the connection, the analyst says he discovered that someone had accessed his computer and opened a folder that held his archived email messages.
During the following hours, while trying to work, the same analyst was disconnected several times from his account. Understanding that something was wrong, the analyst logged the attacker’s unique identifier used to connect to his work computer.
The next day, the analyst provided this identifier to the company’s security team, who quickly tied it to Zhang’s computer. KCG admins revoked Zhang’s access, called in authorities, and started an official investigation.
Zhang stole proprietary source code
This investigation revealed that starting December 2016, when Zhang was promoted to his supervisor role, the suspect installed malware on the company’s servers to record credentials for other users.
After a review of Zhang’s entire activity, KCG says it found evidence that Zhang had used these credentials to access and steal parts of the source code of the company’s trading platform and trading algorithms.
Zhang was able to successfully steal this source code without triggering any security alerts because in December 2016, when he was promoted to a supervisor role, he also got access to the company’s Unix-based network infrastructure.
Because of this, he was able to identify and avoid proxy servers tasked with sniffing network traffic. Because these servers were managed by a third-party company, Zhang rerouted traffic to backup proxy servers, managed by KCG, to hide the data transfers that exfiltrated the proprietary source code to a remote server.
Zhang confessed to fellow employee
After KCG cut off Zhang’s access to all his work accounts on Sunday, the next day, on Monday, Zhang admitted his wrongdoings in an email sent to a KCG employee, Zhang’s former supervisor.
According to the email, obtained by the FBI, Zhang said he knew this [blocking of his accounts] “would happen because [of] what I did in the past few days and Saturday.”
“I am still questioning myself why I did that,” Zhang added.
In the email, Zhang admitted to planting malware on the company’s servers and remotely accessing the accounts of several other KCG employees, besides the quantitive analyst who initially detected his actions.
Zhang says he feared for his job
The email then continued with Zhang explaining to the other KCG employee that he took these extreme actions because he heard of a potential acquisition and feared he would lose his job after the acquisition’s completion.
He started hacking other employees looking for more information on the company’s plans. Yet, this doesn’t explain why he stole the company’s source code.
On Friday, April 7, Virtu Financial, Inc. agreed to purchase KCG for almost $1.4 billion.
The Department of Justice charged Zhang with one count of theft of trade secrets, which carries a maximum sentence of 10 years in prison and a maximum fine of $250,000 or twice the gross gain or loss from the offense.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











