Wcry uses weapons-grade exploit published by the NSA-leaking Shadow Brokers.
A highly virulent new strain of self-replicating ransomware shut down computers all over the world, in part by appropriating a National Security Agency exploit that was publicly released last month by the mysterious group calling itself Shadow Brokers.
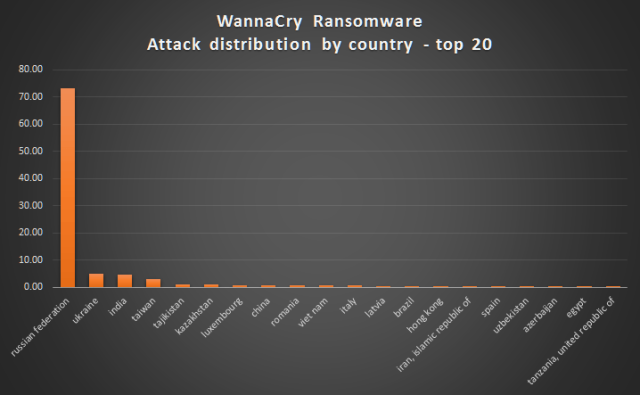
The malware, known as Wanna, Wannacry, or Wcry, has infected at least 75,000 computers, according to antivirus provider Avast. AV provider Kaspersky Lab said organizations in at least 74 countries have been affected, with Russia being disproportionately affected, followed by Ukraine, India, and Taiwan. Infections are also spreading through the United States. The malware is notable for its multi-lingual ransom demands, which support more than two-dozen languages.
Wcry is reportedly causing disruptions at banks, hospitals, telecommunications services, train stations, and other mission-critical organizations in multiple countries, including the UK, Spain, Germany, and Turkey. FedEx, the UK government’s National Health Service, and Spanish telecom Telefonica have all been hit. The Spanish CERT has called it a “massive ransomware attack” that is encrypting all the files of entire networks and spreading laterally through organizations.
The virally spreading worm was ultimately stopped when a researcher who uses the Twitter handle MalwareTech and works for security firm Kryptos Logic took control of a domain name that was hard-coded into the self-replicating exploit. The domain registration, which occurred around 6 AM California time, was a major stroke of good luck, because it was possible only because the attackers had failed to obtain the address first.
The address appeared to serve as a sort of kill switch the attackers could use to terminate the campaign. MalwareTech’s registration had the effect of ending the attacks that had started earlier Friday morning in other parts of the world. As a result, the number of infection detections plateaued dramatically in the hours following the registration. It had no effect on WCry infections that were initiated through earlier campaigns.
Remember Code Red?

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.