Identical code ties Friday’s attacks to hacks on Sony Pictures and $1bn bank heist.
A researcher has found digital fingerprints that tie the WCry ransomware worm that menaced the world on Friday to a prolific hacking operation that previously generated headlines by attacking Sony Pictures, the Bangladesh Central Bank, and South Korean banks.
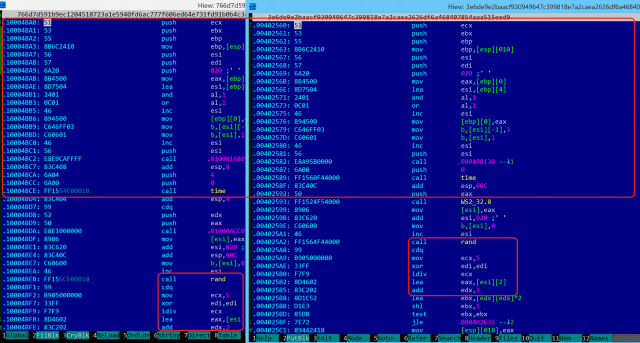
The link came in a cryptic Twitter message from Neel Mehta, a security researcher at Google. The tweet referenced identical code found in a WCry sample from February and an early 2015 version of Cantopee, a malicious backdoor used by Lazarus Group, a hacking team that has been operating since at least 2011. Previously discovered code fingerprints already tied Lazarus Group to the highly destructive hack that caused hard drives in South Korea to self-destruct in 2013, wiped almost a terabyte’s worth of data from Sony Pictures in 2014, and siphoned almost $1 billion from the Bangladesh Central Bank last year by compromising the SWIFT network used to transfer funds.
The missing link
The haystack needle Mehta presented Monday now connects Lazarus to WCry, although the tie connecting the two isn’t precisely clear just yet. WCry’s creators may have deliberately added code found in Cantopee in an attempt to trick researchers into mistakenly believing Lazarus Group is behind the ransomware. Researchers at antivirus provider Kaspersky Lab said such a “false flag” is plausible but improbable. The Cantopee code snippet, the researchers explained, was removed from later versions of WCry, making it hard to spot and hence ill-suited to act as a decoy.
“For now, more research is required into older version of WannaCry,” the Kaspersky Lab researchers wrote in a blog post headlined “WannaCry and Lazarus Group—the missing link.” “We believe this might hold the key to solve some of the mysteries around this attack. One thing is for sure—Neel Mehta’s discovery is the most significant clue to date regarding the origins of WannaCry.”
Little is known about Lazarus Group. It first came to light in a report published in February by security firm Novetta. Kaspersky Lab has authored reports here and here that further document the group, including its ties to North Korea. In early 2015, the Obama administration took the unusual step of sanctioning North Korea after saying US intelligence sources were confident the rogue nation was responsible for the Sony hack.
Other researchers agreed that the shared code between WCry and Cantopee was important.
“This opens a lot of possibilities for everyone to find other similarities between all versions of WannaCrypt that have been found so far, and the tools used by Lazarus,” Maarten van Dantzig, a researcher at FOX-IT, told Ars.
A tie to North Korea might explain some of the unusual behavior researchers have observed in last Friday’s outbreak. The malware came with a mechanism hard-coded into it that allowed the attackers to shut down the self-replicating chain of attacks. Such “killswitches” are highly unusual for malware developed by financially motivated criminal groups. By contrast, they’re much more common in malware written by nation-sponsored hackers.
“Malware authors rarely wonder ‘What if this totally gets out of hand?'” Martijn Grooten, a security researcher for Virus Bulletin, told Ars. “Killswitches in malware are rare, and I can only think of government malware with those built in. Governments care about collateral damage far more than criminals do. And North Korea has recently been active as the Lazarus group.”
Grooten went on to say, “BTW, ‘North Korea’ may well be a foreign hacker group paid by them.”
A North Korean origin might also explain why the malware was fraught with other unusual behavior, including the failure to secure the domain name that triggers the killswitch. Another oddity, as reported by Wired, was WCry’s failure to automatically verify when victims have paid a Bitcoin ransom. If an enemy nation is behind the attack, the motivation may be to sow disruption and anxiety or to embarrass the NSA, rather than to make financial gains.
Readers should know that the usual caveats apply about hacking attribution being fraught with potential errors. A vocal group of critics have long cast doubt on North Korea being behind the Sony attacks. Virtually all of the evidence made public so far is extremely circumstantial. But as Kaspersky and van Dantzig say, the connection disclosed Monday is potentially significant enough to warrant a major worldwide investigation that almost certainly started within minutes of Mehta issuing his tweet.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











