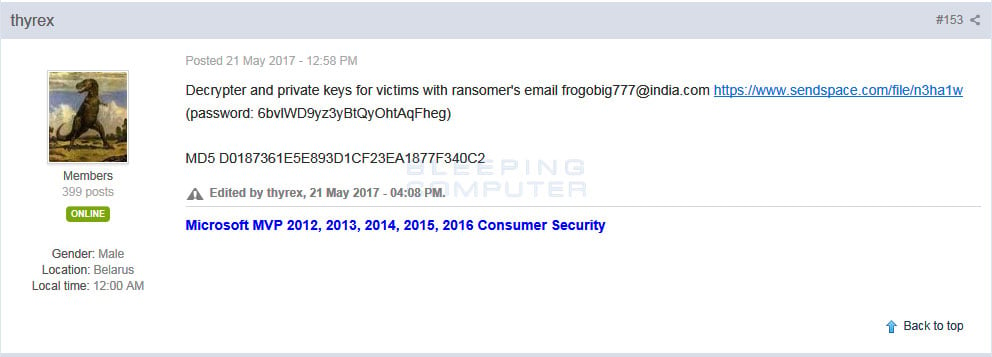
On May 21st, a security researcher who goes by the name Thyrex, received a message on a Russian forum that contained a link to a ZIP file that supposedly contained a decryptor for the frogobig777@india.com variant of the AES-NI Ransomware. After examining the file, Thyrex posted a link to the file in our AES-NI Support Topic so that victim’s could hopefully use it to recover their files.
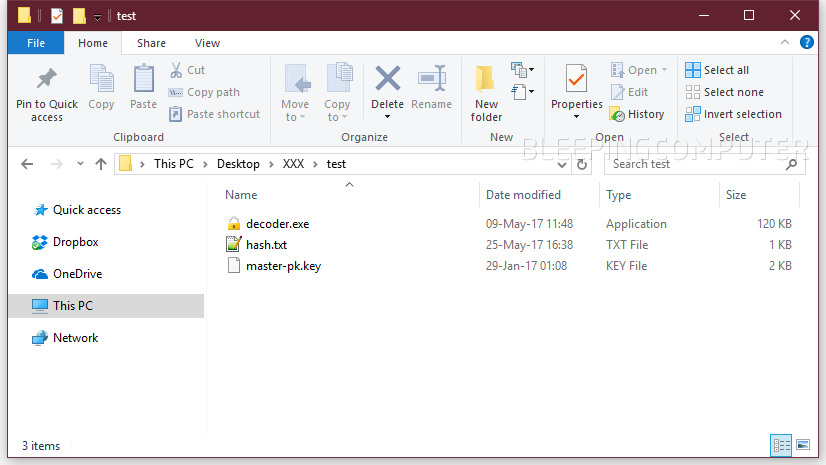
Insider this folder are three files; a decryptor executable, a text file that contains instructions, and a folder of 369 private decryption keys.
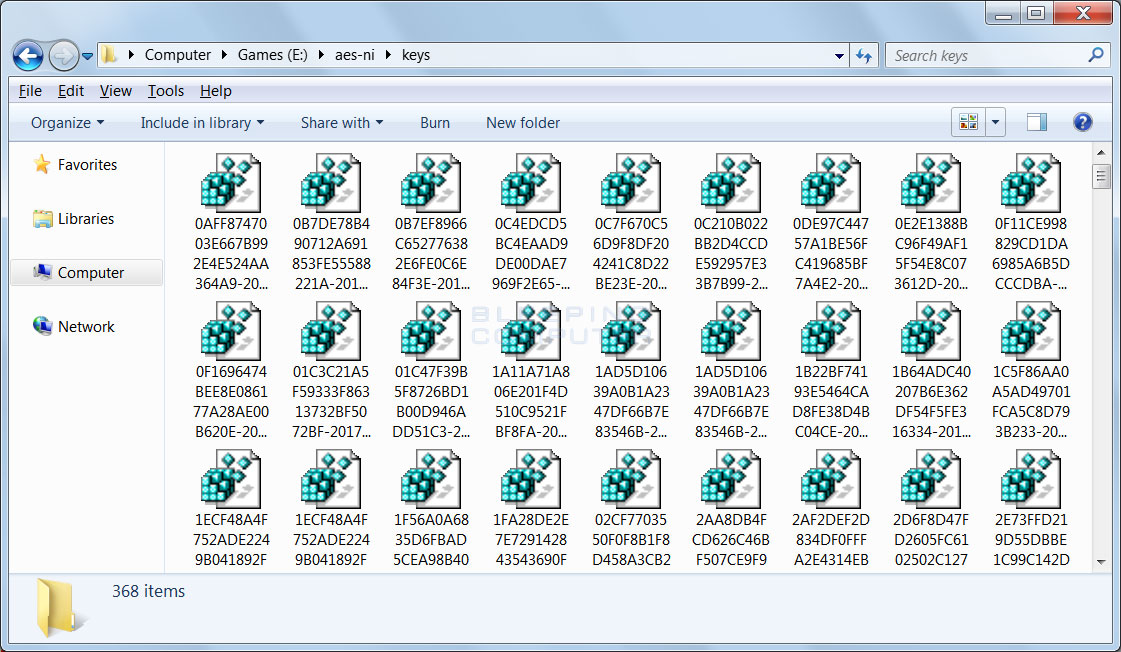
While no victim’s have reported that the decryptor worked for them, I have been able to find an encrypted file from this variant and decrypt it using one of the included keys. If anyone has their files encrypted and the ransom note contains a contact email of frogobig777@india.com, they should definitely see if their key is in the archive and use it to recover their files.
As always, if anyone needs help they can ask in the dedicated AES-NI Ransomware Help & Support Topic.
Who leaked the decryption keys?
Today, BleepingComputer reached out to Thyrex to find out how he received the decoder and keys. According to Thyrex, all that he knew was that an unknown person sent him a private message on a forum he visits with a link to the file.
Coincidentally, the developer of AES-NI, who has been silent for a while, reached out today to various researchers and BleepingComputer to announce he was back. In conversations with BleepingComputer, the AES-NI developer admitted that he was the one who leaked the keys to Thyrex.
He said he did it because it was an old version that a friend of his was previously distributing and abandoned. He also intimated that he would be stopping the AES-NI “project” and releasing the rest of the keys in the near future.
When BleepingComputer asked why he was stopping the development of AES-NI, the developer starting talking about the XData ransomware.
AES-NI author thinks he is being framed by the XData devs
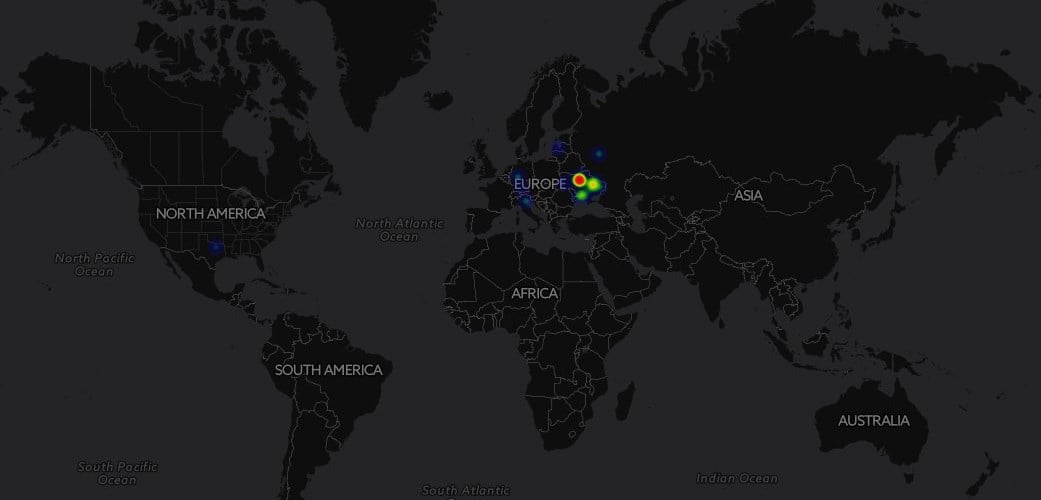
According to the AES-NI developer, XData is based on AES-NI Ransomware source code that someone stole from him between February and March 2017. The shared code between XData and AES-NI was further confirmed by ESET security researcher Anton Cherepanov in an article released yesterday.
It is common for Russian developers to put in restrictions restrictions in their ransomware that prevent the ransomware from infecting victims located in Russia and the Commonwealth of Independent States (CIS). This is done out of a sense of national pride and to protect the developer from a government who may be willing to turn a blind eye to illegal operation that doesn’t target its citizens.
According to the AES-NI author, these restrictions were removed from the XData source and was used to purposely target the Ukraine and other nearby countries. The AES-NI author went on to further state that XData does not contain certain features, such as a TOR Command & Control server and the ability to inject itself into another running process.
The author went on to say that current versions of AES-NI embed the filename and key ID into the encrypted file, while XData does not. As these features were not added until end of March, the author feels that his code was stolen before then.
The AES-NI developer further went on to say that he feels he is purposely being framed by the XData ransomware operator(s). Optimally, he would like that others consider the XData strain a separate operation, despite similarities with the AES-NI source code.
Whether or not any of this true is impossible to corroborate, but if it is true, hopefully the fear of being sent to a Russian prison, or worse, may be enough for the AES-NI dev to keep his promise to stop working on the AES ransomware project and release the rest of the decryption keys.
UPDATE: Minutes after our article went live, the AES-NI author kept his promise and published what appears to be a master decryption key for other ransomware variants. We’ll update the post when we can confirm the validity of this master key. Developing story.
Source:https://www.bleepingcomputer.com/news/security/aes-ni-ransomware-dev-releases-decryption-keys-amid-fears-of-being-framed-for-xdata-outbreak/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











