An investigation by Mexican NGOs and a Canadian tech lab has revealed how the Mexican government is illegally targeting the mobile phones of journalists, lawyers and activists to spy on them.
R3D, SocialTic, Article 19 and CitizenLab report that the government has been sending malware links to specific individuals’ phones, typically with highly personalized messages – even moving on to their family members if they are not duped into clicking.
The attempts have almost certainly been carried out without proper judicial review and use software developed by Israeli company NSO Group called Pegasus, which is sold exclusively to governments.
The malware works by exploiting zero-day holes in common operating systems such as iOS and Android. Individuals are sent text messages or emails and enticed into clicking a link.
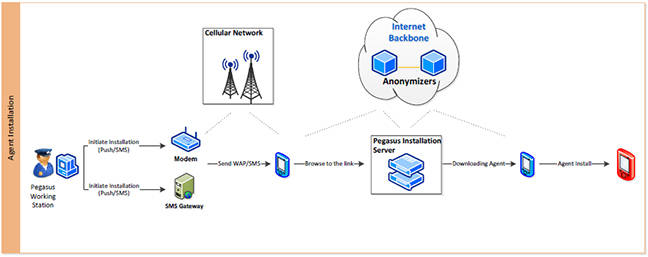 Pegasus process for installing spyware on phones
Pegasus process for installing spyware on phones
The malware messages in Mexico have ranged widely: from pretending to be news articles of interest to the individual, to claimed pictures of armed men outside their house, to a purported video of the husband of one of the targets having sex with a co-worker.
There were fake child abduction alerts, messages purporting to come from the US Embassy in Mexico, fake phone bills – anything and everything likely to pique interest and get a victim to click on the accompanying link.
The targets of these efforts, which include journalists reporting on corruption as well as investigators and human rights lawyers looking at atrocities, have gotten used to the attempts to break into their phones, but a number report having clicked on links and being surprised that they had arrived at a blank page.
How it works
Behind that blank page, however, is a server containing NSO Group’s Pegasus software. The server recognizes the operating system running on the phone and responds with a zero-day exploit that jailbreaks it.
In an investigation by CitizenLab, a chain of three zero-day exploits was noticed – one opening the door for the next – with the end result that an external third party is able to access the phone’s camera and microphone as well as log any messages sent and track the location of the phone.
The investigators are confident that the messages sent to the Mexican journalists and lawyers came from the government, due to the way that the Pegasus system works: it needs to be installed by the company on a specific server, and NSO Group has a strict government-only policy.
The company was started in Israel in 2010 by former members of the country’s elite 8200 intelligence unit. It has changed its name several times, most recently when US private equity fund Francisco Partners bought a majority stake in it for $120 million. It has an annual turnover of $75m and has 150 employees, according to its LinkedIn page.
In return for its spying equipment, the company is well paid. The New York Times reported back in September that NSO Group charges a $500,000 installation fee and then a per-device fee: $650,000 for 10 users; $800,000 for 100. You can keep paying from there upwards: 10 more for $150,000; 20 for $250,000; 50 for $500,000.
Symbian users are the cheapest at $60,000 per user; iPhone and Android are a little more expensive at $65,000 per user; and Blackberries top the list at $100,000 per user. There is an annual system maintenance fee of 17 per cent of the total price.
Company documents say the system offers “unlimited access to a target’s mobile devices” and claims that it “leaves no traces whatsoever.”
Play nice
Although the company asks for assurances from its customers that they will use its system solely for tackling criminal activity and terrorism, it is powerless to prevent those with the equipment from using it on whomever they wish.
If they did wish to cut a government off – which in itself would be a tough call – NSO Group could only refuse to keep sending updates to the system so that over time its ability to work would tail off, as companies like Google and Apple find holes and patch them.
The Mexican NGOs that carried out the investigation have no doubt that unofficial forces within the Mexican government are authorizing the hacks, almost certainly without going through the proper process of judicial review. Those targeted stand out for being outspoken critics of corruption within the government.
“The infection attempts often coincided with work on specific high-profile investigations and sensitive issues,” noted CitizenLab. The Mexican government denies any knowledge of the hacks.
Source:https://www.theregister.co.uk/2017/06/19/mexican_gov_accused_of_phone_hacking_citizens/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











