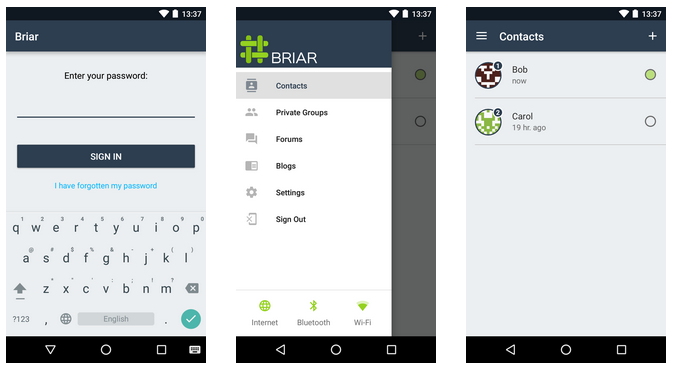
Briar, an instant messaging service that works over the Tor network, has reached beta stage today, the app’s creators announced.
Only an Android app is available at the moment, which users can download from the Google Play Store here.
Briar passes security audit
The Briar team also announced the conclusion of a security audit performed by Cure53, the same organization that reviewed other services such as SecureDrop, Cryptocat, and Dovecot.
The conclusion of the security audit is that Briar for Android provides “an overall good handling of matters linked to security and privacy.” Furthermore, the code responsible with the app’s cryptography “was found to be exceptionally clear and sound, with no vulnerabilities spotted,” said Cure53 in their report.
All bugs discovered during the audit were fixed in the Briar app’s beta version currently available on the Play Store.
Briar app works via Tor, Bluetooth, and WiFi
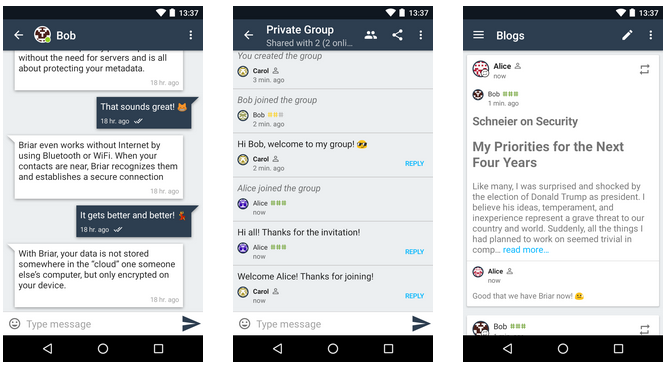
Activists, journalists, and anyone who needs a safe way to communicate in private will love Briar.
Under the hood, Briar uses a peer-to-peer system with no central servers to relay information. People who communicate using Briar exchange messages directly with each other.
All communications are end-to-end encrypted, use forward secrecy, and don’t carry any metadata (which is somewhat important, some might say). Briar is also censorship resistant. This is because there are no central servers that a government can block to take down the entire service.
By default, Briar uses Tor to exchange messages between two users. In case local governments block Tor, the app will continue to function and exchange messages using nearby WiFi networks or local meshes of Bluetooth connections.
No rush to deliver a stable version
Bleeping Computer spoke to Torsten Grote, one of the app’s developers. According to the developer, there is no fixed release date for a stable version. This is mainly because Briar is open-source, with no commercial backing and strict deadlines. Nobody’s in a hurry to deliver a rushed and incomplete app just to tick a checkmark.
“Like with many Free Software projects, it will be done when it is done,” said Grote, who also added that there are plans for a desktop app for the future.
“Briar is built as modular as possible,” he says. “There are two libraries that can be used to build apps on top of them. We definitely want to do a desktop app.”
“An iOS app is trickier because iOS is more closed than Android,” Grote added. “There are heavier restrictions on background services for example that are required for P2P apps.” Nonetheless, the team is thinking about an iOS version, especially after users have requested one.
Current development plans are focused on improving Briar for Android before its official release.
“We are currently collecting issues to address for a second beta release,” Grote told Bleeping Computer. “Our private beta testers were mostly worried about two things: battery usage and the ability to add contacts remotely.”
I2P support may arrive in a future version
Other future plans include a secondary option to use I2P as an alternative to Tor for the app’s data transport layer.
“It is worth noting that Briar is agnostic to the data transport that is used,” Grote told Bleeping. “If tomorrow, there is something better than Tor, we can easily use that.”
Briar has already garnered a reputation and nickname with privacy enthusiasts. The app is sometimes referred to as Darknet Messenger.
The Tor Project also releases its own Tor-based messenger app called Tor Messenger, but the app is only available for Linux, Mac, and Windows, with no Android version. Here is where Briar can help.
Despite being competitors on the IM market, the two projects seem to be friends.
“Our developers know many of the Tor developers and they know us,” Grote said. “We discuss issues like battery usage of Tor on mobile devices and work together to improve that.” Outside this, there are no official or financial connections between the two projects.
Source:https://www.bleepingcomputer.com/news/security/briar-tor-based-messenger-passes-security-audit-enters-beta-stage/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











