On Friday, an unknown hacker hijacked the Copyfish Chrome extension from its original authors and pushed an update that inserted ads in people’s web pages.
The hack took place because one of the Copyfish developers fell for a simple phishing trick and accessed a link in an email he thought he received from the Chrome team.
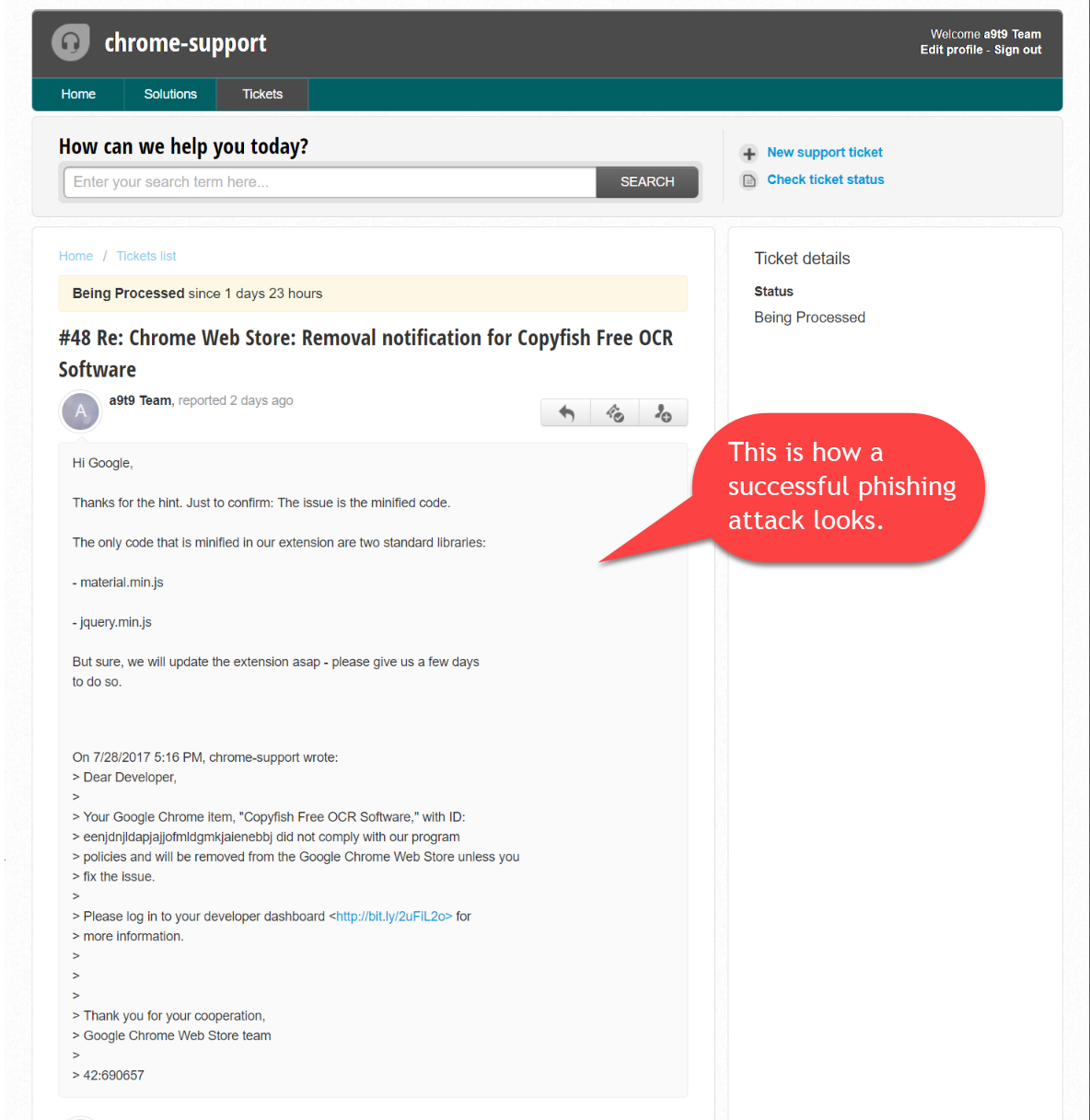
In reality, the email came from the phisher and urged the Copyfish developer to update his extension, or it would be removed from the Chrome Web Store.
Developer fell for simple phishing trick
When the developer accessed the link, he was redirected to a copy of the Google account login page, where the Copyfish dev entered the credentials of the Copyfish developer account.
The login page was hosted on chromedev.freshdesk.com, and surprisingly the extension’s developer didn’t think it was strange, even if Google has hosted its support desks on its own domains for more than a decade.
On Saturday, a day later, the hacker had pushed a malicious update (v2.8.5) for the Chrome Copyfish extension, which a pretty powerful tool for extracting text from images and PDF files.
Malicious update inserted ads in people’s browsers
The update added extra JavaScript code that loaded ads on all the pages a user viewed. Despite this intrusive behavior, it took Copyfish developers a full day to realize what had happened.
Unfortunately, by that point, the hacker had transferred the extension to his own developer account, out of the reach of the original authors, who were desperately trying to reach a Google staffer to have the extension pulled down.
On Monday, a post-mortem blog post published by the Copyfish team reached the Hacker News news aggregator service. This extra exposure helped the Copyfish team get in contact with Google employees but also contributed to stopping the hijacked extension’s adware behavior after the owner of the Unpkg CDN service had taken down malicious JavaScript files used by the extension.
At the time of writing, the extension is still under the hijacker’s control. Users are advised to remove it from their browsers. The Copyfish team says its Firefox add-on is safe and under their control.
Source:https://www.bleepingcomputer.com/news/security/copyfish-chrome-extension-hijacked-to-show-adware/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











