Metadata from web traffic generated by smart devices installed in a home can reveal quite a lot of information about the owner’s habits and lifestyle.
According to research published this month by experts from Princeton University, a determined attacker with “capabilities similar to those of an ISP” can use passive network monitoring techniques to collect metadata exchanged by locally installed IoT devices and their remote management servers.
Even if encrypted or tunneled through a VPN, the traffic leaks enough metadata for an attacker to infer various details about the device’s owner.
IoT devices recognizable via DNS requests, MACs, traffic patterns
The leaks happen via so-called “traffic flows” between IoT devices and their remote servers, flows that are easy to recognize via various patterns. The easiest way to identify these traffic flows is via DNS requests, unique to each of the smart devices.
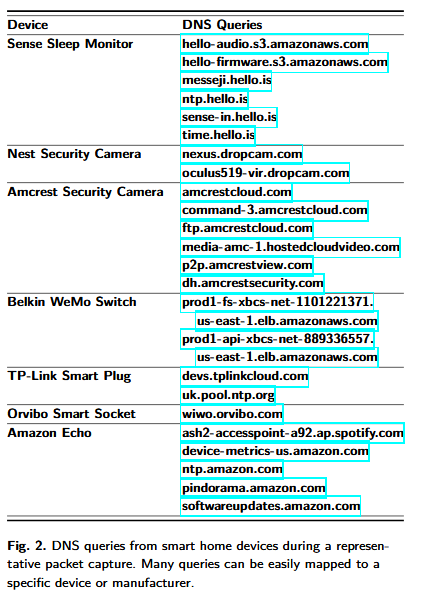
Other ways to identify traffic flows are via the first six digits of MAC addresses (the organizational unique identifier) and traffic rates — patterns of repetitive queries to the device’s remote management servers.
Attack proven successful in practice
To prove their point, researchers experimented with seven IoT devices and using the techniques above they tried to infer details about the devices’ owner.
2. Nest Cam Indoor security camera
3. Amcrest WiFi Security IP Camera
4. Belkin WeMo switch
5. TP-Link WiFi Smart Plug
6. Orvibo Smart WiFi Socket
7. Amazon Echo
Researchers say they were able to determine when the owner was at home by spikes in activity from devices such as Amazon Echo and WiFi plugs.
In addition, researchers were also able to identify when the owner was sleeping by the increased activity in the Sense sleep monitor, who became more active when it had to collect data about the user’s sleeping activity.
Similarly, researchers say they could detect when the user was away from home because of spike-like patterns in the traffic of Nest cams, which uploaded snapshots to remote servers at regular intervals. This happened only when the owner was away and activated the camera’s surveillance mode.
IoT’s “always on” model is to blame
The Princeton research crew warns users not to underestimate the efficiency of this type of attack. The warning comes because most IoT devices cannot work without an Internet connection, and some of them are intentionally designed to function this way.
From the seven devices researchers tested for their experiment, three ceased to function once taken offline, and four worked, but in a very limited capacity. This means that if users purchased these devices, they are most likely using them to their full capability and keeping them connected online all the time.
This leaves a constant footprint that attackers can watch and use it to silently track users in their homes, thanks to the traffic generated by the IoT devices.
Simple mitigation exists
Fortunately, researchers say there’s a simple technique that can safeguard users against these passive monitoring attacks.
“Our experiments show that traffic shaping can effectively and practically mitigate many privacy risks associated with smart home IoT devices,” researchers say.
By “traffic shaping” researchers are referring to a practice of inserting dummy network requests at random intervals. These requests hide real activity and keep attackers in the dark.
Researchers say that for smart homes without audio or video streaming capabilities, the fake traffic takes up only a maximum of 7.5 KB/s of the user’s normal Internet bandwidth. For smart home devices with audio and video streaming, the fake traffic bandwidth goes up to 40 KB/s. Both values are more than acceptable, especially for users with broadband connections.
We hope that consumers will become better aware of smart home privacy vulnerabilities and incentivize manufacturers to more carefully consider privacy issues in the design of their products. While our proposed traffic shaping solution is practical and sufficient, improved regulation of ISPs and other passive network observers may also be necessary to offset the unique privacy challenges posed by IoT devices.
For more details on this topic, we recommend reading the research paper at the base of this article, entitled “Spying on the Smart Home: Privacy Attacks and Defenses on Encrypted IoT Traffic,” by Princeton University researchers Noah Apthorpe, Dillon Reisman, Srikanth Sundaresan, Arvind Narayanan, and Nick Feamster.
Source:https://www.bleepingcomputer.com/news/technology/metadata-from-iot-traffic-exposes-in-home-user-activity/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











