Mobile security experts from Palo Alto Networks have detailed a new attack on Android devices that uses “Toast” notifications to help malware in obtaining admin rights or access to Android’s Accessibility service — often used to take over users’ smartphones.
During the past few years, most of the top Android malware has used the same trick to get full control over a user’s device.
That trick relied on malware fooling users during an app installation process to grant it the permission to display content on top of other apps — via the “Draw on top” permission.
Once malicious apps obtained this permission, they would use it to display intrusive popups on the user screen, asking the user to confirm some message or take some action. In reality, the app would request access to the Android Accessibility service but use the “Draw on top” permission to display fake messages on top of the “Activate” button.
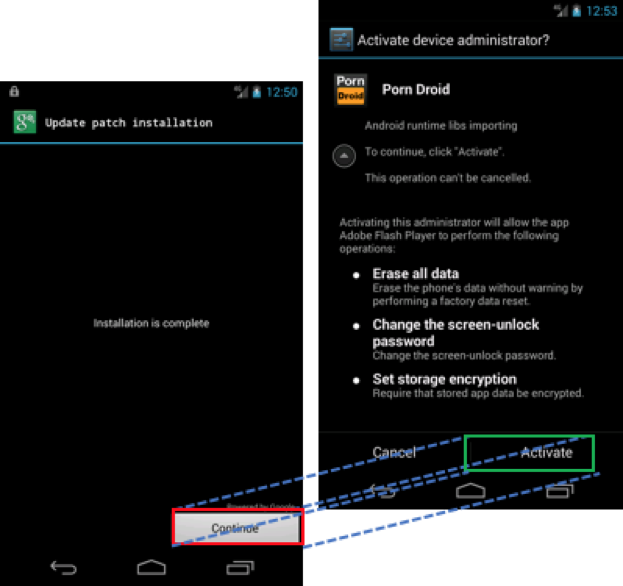
Similarly, malicious apps would use the same “Draw on top” permission to display fake content on top of the popup that grants the attacker admin rights.
This technique was known and used in live attack for at least two years but was explained for the first time in depth in a research paper named “Cloak & Dagger,” a name that’s now used to describe this entire attack routine.
New variation of the Cloak & Dagger attack
Palo Alto experts say this research paper inspired them to look into other ways to carry out Cloak & Dagger attacks.
Their explorations led them to Toast messages, which are short-lived popups that appear at the bottom of the screen. The Android OS and many apps use this notification to display self-fading messages, like the ones that appear when Gmail confirms the sending of a message or the user connects to a WiFi network.
Palo Alto researchers say that attackers can use Toast messages to carry out a variation of the Cloak & Dagger attack.
Toast messages are useful for attackers because they inherently appear above any other applications, and do not require a malicious app to get the “Draw on top” permission during its installation process.
An attacker only needs to fool a user into installing a malicious app on their phone. They can then ask for admin rights or access to the Accessibility service, but mask confirmation buttons or other description text with customized toast messages.
Instead of seeing an “Activate” button, attackers can use Toast messages to make the button say “Continue,” instead.
Further, researchers say that an attacker can loop Toast messages to appear continuously, masking legitimate content for as long as it’s necessary.
“The Toast attack requires fewer explicit user steps to exploit and also can be exploited by apps that don’t come from Google Play,” Christopher Budd, Senior Manager of Cybersecurity and Threat Intelligence at Palo Alto Networks, told Bleeping Computervia email. “Taken together these make this vulnerability more broadly viable for possible attacks.”
All Android versions up to 7.0 are affected
Palo Alto says all versions of Android, except the latest (Android 8.0 Oreo), are vulnerable to Toast overlay attacks.
Researchers reported the issue to Google at the end of May, and Google responded by requiring apps that use Toast messages to ask for the “Draw on top” permission, like everyone else.
The issue — tracked as CVE-2017-0752 — was patched on Tuesday, when Google released the September 2017 Android Security Bulletin. Android OS versions with the September 2017 security patch levels are safe against Toast overlay attacks. A video of a Toast overlay attack is available on Palo Alto’s website.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











