A Russian-speaking hacker has been infecting Netgear routers over the past months with a new strain of malware named RouteX that he uses to turn infected devices into SOCKS proxies and carry out credential stuffing attacks.
According to Forkbombus Labs, the US cyber-security firm that uncovered this new threat, the hacker is using CVE-2016-10176, a vulnerability disclosed last December to take over Netgear WNR2000 routers.
CVE-2016-10176 is a vulnerability that affects the web server included with Netgear WNR routers, which is responsible for powering the device’s built-in administrative interface. The vulnerability allows unauthenticated attackers to perform sensitive, admin-level actions.
RouteX malware transforms Netgear routers into proxies
Stu Gorton, Chief Science Officer and Head of Research of Forkbombus Labs, says the attacker uses the vulnerability to download and run the RouteX malware on Netgear routers running older, vulnerable firmware.
The RouteX malware has two main functions. The first is to install a SOCKS proxy on each infected device.
The second is to add iptable (Linux firewall) rules that prevent further exploitation of the same vulnerability, but also restrict access to the device to a few IP addresses, most likely under the attacker’s control.
Netgear routers used for credential stuffing attacks
The hacker uses the hijacked Netgear routers to perform credential stuffing attacks — automated operations in which a threat actor takes credentials from publicly leaked data breaches and tests username and password combos on a multitude of online services in rapid succession.
The proxies installed on Netgear routers allow the attacker to spread his credential stuffing attack to new IPs and avoid getting banned by any brute-force protection systems that any of his victims may be running.
Gorton says that most of the targets of these credential stuffing attacks are Fortune 500 companies.
“Unfortunately we cannot reveal the targets of the credential stuffing attacks themselves due to our relationships and position in the investigation,” Gorton told Bleeping Computer in an email.
“[But] we have observed victims of the credential stuffing attacks sending cease and desist letters to those who are infected by the RouteX malware,” Gorton added.
The size of this botnet made up of Netgear routers is currently unknown.
“This is largely because the infected devices do not maintain a persistent connection to the C2 infrastructure,” Gorton told Bleeping, revealing the attacker connects to devices only when he needs to.
RouteX malware linked to hacker “Links”
Based on ten command-and-control domain names Fokbombus Labs found inside the RouteX malware source code, researchers were able to connect the malware to emails used in the past by a hacker who goes on the Exploit.in forum by the nickname of Links.
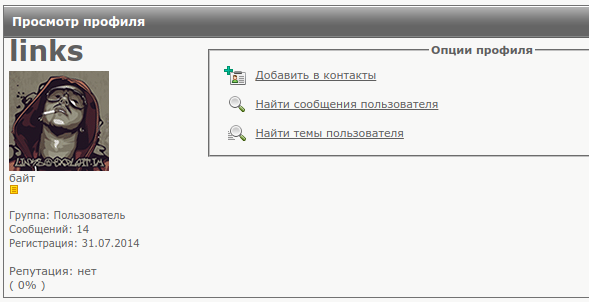
Forkbombus Labs says Links is also the author of the eponymous Links malware that has infected Ubiquiti Networks devices in October 2016.
According to Gorton, the malware also works as a proxy system, is a predecessor of the RouteX malware, and is far less complex. Another connection to RouteX is that the Links malware uses a similar ASCII-based splash screen when logging in.
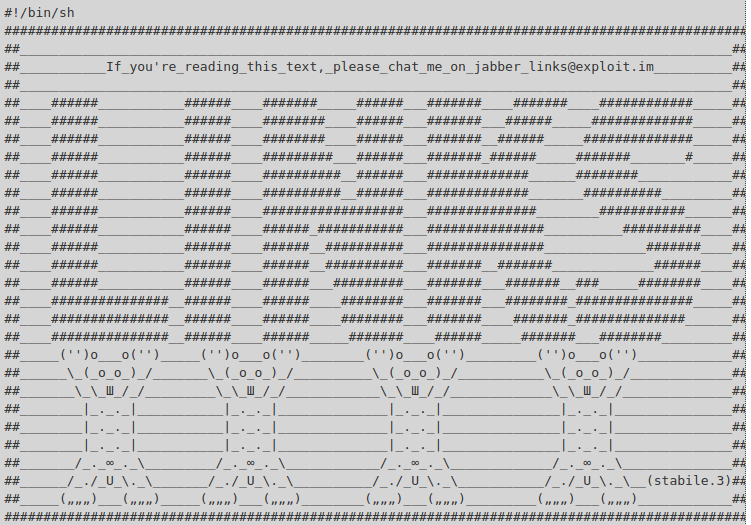
Indicators of compromise and a step-by-step walkthrough on how Forkbombus Labs experts tracked down the RouteX malware author are available in a report released last week.
Owners of Netgear WNR2000 router models are advised to install the latest firmware version. To stay safe from credential stuffing accounts, users should avoid reusing passwords across different sites.
Source:https://www.bleepingcomputer.com/news/security/routex-malware-uses-netgear-routers-for-credential-stuffing-attacks/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











