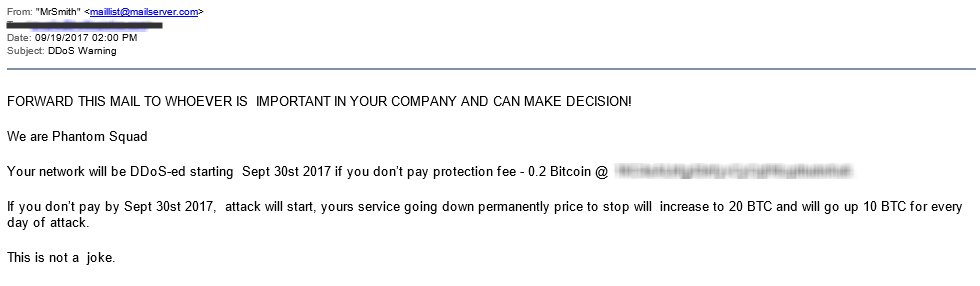
A group of DDoS extortionists using the name of Phantom Squad has sent out a massive spam wave to thousands of companies all over the globe, threating DDoS attacks on September 30, if victims do not pay a ransom demand.
The emails spreading the ransom demands were first spotted by security researcher Derrick Farmer and the threats appear to have started on September 19 and continued ever since.
Hackers looking for small $700 ransoms
The emails contain a simple threat, telling companies to pay 0.2 Bitcoin (~$720) or prepare to have their website taken down on September 30.
Usually, these email threats are sent to a small number of companies one at a time, in order for extortionists to carry out attacks if customers do not pay.
This time, this group appears to have sent the emails in a shotgun approach to multiple recipients at the same time, a-la classic spam campaigns distributing other forms of malware.
Because of this, several experts who reviewed the emails and ransom demands reached the conclusion that the group does not possess the firepower to launch DDoS attacks on so many targets on the same day, and is most likely using scare tactics hoping to fool victims into paying.
Extortionists are not the sharpest tool in the shed
The size of this email spam wave is what surprised many experts. Its impact was felt immediately on social media [1, 2, 3, 4] and on webmaster forums, where sysadmins went looking for help and opinions on how to handle the threat.
Bleeping Computer reached out to several security companies to get a general idea of the size of this spam wave.
“Not sure how widespread it is in terms of volume, but they are certainly spamming a lot of people,” Justin Paine, Head of Trust & Safety at Cloudflare, told Bleeping.
“We’ve had 5 customers so far report these ‘Phantom Squad’ emails,” he added. “These geniuses even sent a ransom threat to the noc@ address for a major DDoS mitigation company.”
Extortionists are “recycling” email text
Radware engineers received similar reports, so much so that the company issued a security alert of its own.
Radware security researcher Daniel Smith pointed out that the extortionists may not be the real Phantom Squad, a group of DDoS attackers that brought down various gaming networks in the winter of 2015 [1, 2].
Smith noticed that the ransom note was almost identical to the one used in June 2017 by another group of extortionists using the name Armada Collective. Those extortion attempts through the threat of DDoS attacks also proved to be empty threats, albeit some were successful.
“The part that I find interesting is the low ransom request compared to the ransom request last month,” Smith told Bleeping Computer. “Last month a fake RDoS group going by the name Anonymousransomed several banks for 100 BTC.”
Experts don’t believe the group can launch DDoS attacks
This shows an evolution in ransom DDoS (RDoS) attacks, with groups moving from targeting small groups of companies within an industry vertical to mass targeting in the hopes of extracting small payments from multiple victims.
“This is what the modern RDoS campaign has come to,” Smith also said. “In the spring of 2016 after a lull in RDoS attacks, a group emerged calling themselves the Armada Collective, but their modus operandi had clearly changed. This group claiming to be Armada Collective was no longer targeting a small number of victims but instead were targeting dozens of victims at once without launching a sample attack.”
“As a result, these attackers were able to make thousands of dollars by taking advantage of public fear and a notorious name. Several other copycat groups that emerged in 2016 and 2017 also leveraged the names of groups like, New World Hackers, Lizard Squad, LulzSec, Fancy Bear, and Anonymous.”
“To launch a series of denial-of-service attacks, this group will require vast resources. Therefore, when a group sends dozens of extortion letters, they typically will not follow through with a cyber-attack,” Smith said.
Smith’s opinion is also shared by Paine, who recently tweeted “ransom demands from this group = spam” and “empty threats, zero attacks from this copycat.”
Victims should report extortion attempts to authorities
Japan CERT has issued a security alert informing companies how to handle the fake demands by reporting the emails to authorities.
Today, security researcher Brad Duncan also published an alert on the ISC SANS forums, letting other sysadmins and security researchers know not to believe the ransom threats.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











