The CSE CybSec Z-Lab Malware Lab spotted a new botnet, dubbed Wonder botnet, while it was investigating malicious code in the dark web.
While investigating the malicious code in the dark web, ZLab experts discovered a “NetflixAccountGenerator.exe” that promises to generate a premium account for Netflix services for free. Unfortunately, the software downloaded does not work as expected because it installs a BOT rather than create a desiderated account!
The malware researchers analyzed this “exe” file and discovered that the malware is not indexed yet: only one site on the Clearnet identified it as a threat after it was uploaded for the first time around September 20th, probably by the author in order to test its ability to remain stealth.
The analysis of the malware revealed it is a bot that belongs to an alive botnet dubbed by the experts Wonder botnet. The Command and Control is hidden behind a site that is the mirror of another one:

Figure 1 – On the left the fake site; on the right the original site
Experts verified that the fake page “support.com” at the link “wiknet.wikaba.com” on the left side, point to the front-end of the botnet’s C2C. The interesting thing is that every link on it refers to the original page, clicking on one links the researchers were redirected to the corresponding page on “support.com”.
The experts also discovered some hidden paths that contain the information and the commands used by the bots.
The malware is composed of two parts:
- A Downloader: it is a .NET executable with the only purpose of downloading and executing the real bot code, uploaded on “pastebin.com/raw/E8ye2hvM”.
- The real Bot: when it is downloaded and executed, it infects the host setting its persistence mechanisms and starts its malicious behavior schematized in the following figure:
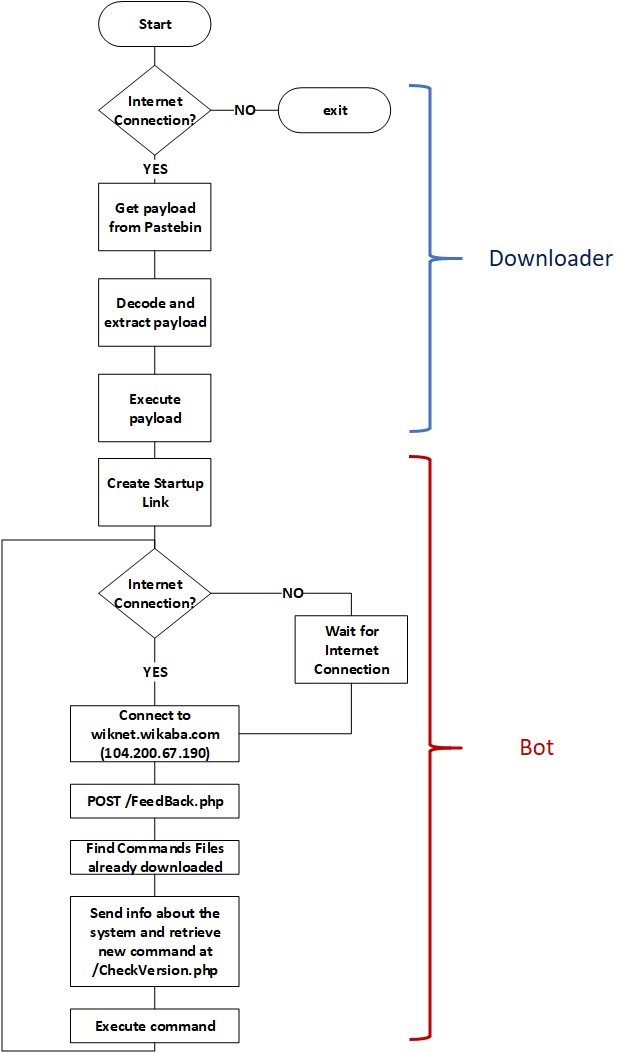
Figure 2 – Wonder Botnet’s behavior scheme
Further technical details, including IoCs and Yara rules are included in the report published by CSE Cybsec ZLab.
Source:https://securityaffairs.co/wordpress/64633/malware/wonder-botnet-dark-web.html

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











