Android apps with millions of Google Play downloads also crash the party.
A researcher has documented almost 2,500 sites that are actively running cryptocurrency mining code in the browsers of unsuspecting visitors, a finding that suggests the unethical and possibly illegal practice has only picked up steam since it came to light a few weeks ago.
Willem de Groot, an independent security researcher who reported the findings Tuesday, told Ars that he believes all of the 2,496 sites he tracked are running out-of-date software with known security vulnerabilities that have been exploited to give attackers control. Attackers, he said, then used their access to add code that surreptitiously harnesses the CPUs and electricity of visitors to generate the digital currency known as Monero. About 80 percent of those sites, he added, also contain other types of malware that can steal visitors’ payment card details.
“Apparently, cyberthieves are squeezing every penny out of their confiscated assets,” he said.
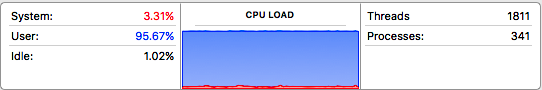
One of the affected sites is shop.subaru.com.au. When I visited the site on Tuesday, the fan on my MacBook Pro, which I hadn’t heard in months, soon started whirring. The activity monitor showed that about 95 percent of the CPU load was being consumed. As soon as I closed the site, the load dropped to about 9 percent. Besides putting a noticeable strain on my computer, the site also draws additional electricity from my office. The arrangement allows the attackers to reap the benefit of my hardware and electricity without providing anything to me in return. A recent report from security firm Trustwave’s SpiderLabs estimated that the electricity cost for a single computer could range from about $2.90 to $5 per month, presumably if the cryptomining page was left open and running continuously over that time. The figure doesn’t include the wear and tear on hardware as it performs complex mathematical problems required to generate the digital coins.
Thanks, Coinhive

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











