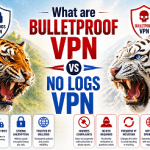
Fruitfly creepware turned on cameras and mics, automatically detected porn searches. Early last year, a piece of Mac malware came to light that left researchers puzzled. They knew that malware dubbed Fruitfly captured screenshots and webcam images, and they knew it had been installed on hundreds of computers in the US and elsewhere, possibly for more than a decade. Still, the researchers didn’t know who did it or why.
An indictment filed Wednesday in federal court in Ohio may answer some of those questions. It alleges Fruitfly was the creation of an Ohio man who used it for more than 13 years to steal millions of images from infected computers as he took detailed notes of what he observed. Prosecutors also said defendant Phillip R. Durachinsky used the malware to surreptitiously turn on cameras and microphones, take and download screenshots, log keystrokes, and steal tax and medical records, photographs, Internet searches, and bank transactions. In some cases, Fruitfly alerted Durachinsky when victims typed words associated with porn. The suspect, in addition to allegedly targeting individuals, also allegedly infected computers belonging to police departments, schools, companies, and the federal government, including the US Department of Energy.
Creepware
The indictment, filed in US District Court for the Northern District of Ohio’s Eastern Division, went on to say that Durachinsky developed a control panel that allowed him to manipulate infected computers and view live images from several machines simultaneously. The indictment also said he produced visual depictions of one or more minors engaging in sexually explicit conduct and that the depiction was transported across state lines. He allegedly developed a version of Fruitfly that was capable of infecting Windows computers as well. Prosecutors are asking the court for an order requiring Durachinsky to forfeit any property he derived from his 13-year campaign, an indication that he may have sold the images and data he acquired to others.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.