Security researchers have revealed details of a vulnerability in WhatsApp’s security that could be used to compromise the secrecy of encrypted group chats on the messaging platform.
The risk associated with the flaw is limited on account of attackers needing to have access to WhatsApp servers to be able to insert themselves into a group conversation.
That said, WhatsApp does continue to face pressure from governments over its use of end-to-end encryption. So any vulnerability that could even theoretically offer a route for the company to be coerced by state entities to collaborate with their agents to afford a degree of access to encrypted conversations is worth highlighting.
Wired reports that the encryption flaws, which were detailed today at the Real World Crypto security conference in Zurich, Switzerland, by a group of researchers from Ruhr University Bochum in Germany, also affect the Signal and Threema messaging apps — though to a lesser degree.
Regarding WhatsApp, the researchers say that anyone who controls WhatsApp’s servers could insert new participants into an otherwise private group without having the permission of the group administrator.
The attack apparently takes advantage of a bug in how WhatsApp handles group chats — in that while only the administrator of a group can invite new members the platform does not use any authentication mechanism for an invitation that its own servers cannot spoof.
Once an attacker with access to a WhatsApp server had added a new member to a group the phone of every participant would automatically share secret keys with that new member — affording them full access to any future messages. (Though messages sent prior to them joining the group would remain unreadable.)
And while everyone in the chat would be notified that a new member has joined, it would likely be up to the administrator to notice and call out a spoofed invite (since they are the users capable of creating invite links).
The researchers also suggest that an attacker with access to WhatsApp servers could selectively block any messages in the group — closing down the ability of group participants to ask questions, or provide warnings about the interloper.
Reached for comment, a WhatsApp spokesman confirmed the security researchers’ findings but said it views the risk as limited because no one can secretly join a WhatsApp group chat — meaning users can always chat one-to-one to confirm any suspicions about unknown members appearing in their groups.
“We’ve looked at this issue carefully,” a spokesman told us. “Existing members are notified when new people are added to a WhatsApp group. We built WhatsApp so group messages cannot be sent to a hidden user. The privacy and security of our users is incredibly important to WhatsApp. It’s why we collect very little information and all messages sent on WhatsApp are end-to-end encrypted.”
The team of security researchers, who revealed the flaw to WhatsApp last July, suggest the company could fix the issue by adding an authentication mechanism for new group invitations that uses a secret key that only the administrator possesses to sign those invitations.
Such added authentication layers would likely made it impossible for WhatsApp to provide group invite links which allow people to quickly add new members to a group — which explains why the company is reluctant to change the system it has in place, despite the apparent element of risk.
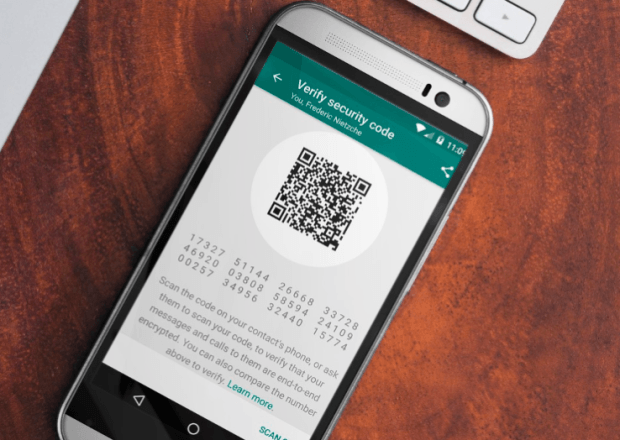
It also points out that WhatsApp users are able to view the membership of a group by tapping ‘group info’, and can verify the security code of individual members for added security.
For the Signal messaging app, which uses the same underlying encryption protocol as WhatsApp, the security researchers found the app contains the same group chat vulnerability but further mitigated by an attacker not only having to control the relevant Signal server but also having to know the Group ID number for the chat (and these IDs are essentially unguessable).
Open Whisper Systems, the non-profit which runs and maintains Signal, is also apparently in the process of redesigning how Signal handles group messaging.
A third encrypted messaging app, Threema, which was also shown to contain some more minor bugs relating to group chats by the researchers, has already put out a fix to patch its software.
Last January another security issue relating to WhatsApp’s platform was highlighted after a security researcher showed it was possible to force the generation of new encryption keys for offline users — reigniting debate over how key verification is implemented within an encrypted system. However WhatsApp said the “retransmission vulnerability” was an intentional design decision aimed at avoiding millions of messages from being lost.
It also pointed out that users can opt to “Show Security Notifications” — which provides them with a notification when a contact’s security code has changed, and thus offers an alert when/if there’s a risk of their messages being man-in-the-middle intercepted.
Source:https://techcrunch.com/2018/01/10/security-researchers-flag-invite-bug-in-whatsapp-group-chats/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.