The South Korean Computer Emergency Response Team issued a warning Wednesday of a new Adobe Flash Player zero-day spotted in the wild. The security bulletin warns that the attacks are focused on South Koreans and involve malicious Microsoft Word documents.
According to the South Korean Computer Emergency Response Team (KR-CERT), the zero-day is believed to be a Flash SWF file embedded in MS Word documents. Impacted is Adobe’s most recent Flash Player 28.0.0.137 and earlier.
“An attacker may be able to convince a user to open a Microsoft Office document, web page, or spam mail containing a Flash file,” according to a machine translation of the KR-CERT security bulletin.
Adobe released a security advisory on Thursday acknowledging the vulnerability and attacks.
“Adobe is aware of a report that an exploit for CVE-2018-4878 exists in the wild, and is being used in limited, targeted attacks against Windows users. Adobe will address this vulnerability in a release planned for the week of February 5,” according the advisory.
Adobe said the zero-day is exploiting the vulnerability CVE-2018-4871, an out-of-bounds read issue. According to Mitre’s CVE record it was discovered in Adobe Flash Player before 28.0.0.137. It rates the threat as “critical”. Adobe credits KR-CERT for reporting this issue.
Adobe said affected products are versions of Adobe Flash Player Desktop Runtime (Win/Mac), Adobe Flash Player for Google Chrome (Win/Mac/Linux/Chrome OS), Adobe Flash Player for Microsoft Edge and Internet Explorer 11 (Win 10 & 8) and Adobe Flash Player Desktop Runtime (Linux). A complete list is available here.
“This vulnerability occurs because of computation that reads data that is past the end of the target buffer. The use of an invalid (out-of-range) pointer offset during access of internal data structure fields causes the vulnerability. A successful attack can lead to sensitive data exposure,” according to the Mitre description of the vulnerability.
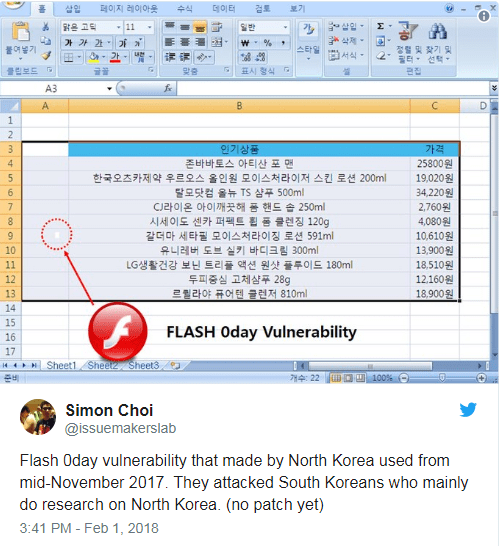
Simon Choi, a security researcher with the South Korean security firm Hauri, claimed on Twitter that the zero-day vulnerability originated in North Korea and has been in use since mid-November 2017. Targeted are South Koreans researching online for information about North Korea.
KR-CERT is recommending users refrain from using Microsoft’s Internet Explorer browser and use Mozilla’s Firefox browser instead.
On Thursday Adobe recommended:“Beginning with Flash Player 27, administrators have the ability to change Flash Player’s behavior when running on Internet Explorer on Windows 7 and below by prompting the user before playing SWF content. For more details, see this administration guide. Administrators may also consider implementing Protected View for Office. Protected View opens a file marked as potentially unsafe in Read-only mode,” Adobe said.
Source:https://threatpost.com/adobe-flash-player-zero-day-spotted-in-the-wild/129742/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.