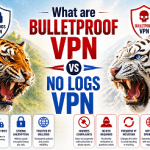
Certificates registered in names of real corporations are surprisingly easy to come by. The Stuxnet worm that targeted Iran’s nuclear program almost a decade ago was a watershed piece of malware for a variety of reasons. Chief among them, its use of cryptographic certificates belonging to legitimate companies to falsely vouch for the trustworthiness of the malware. Last year, we learned that fraudulently signed malware was more widespread than previously believed. On Thursday, researchers unveiled one possible reason: underground services that since 2011 have sold counterfeit signing credentials that are unique to each buyer.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.