It was recently revealed by information security training researchers that an analytics firm, Cambridge Analytica, wrongfully gained access to the data of 50 million people swept up from Facebook via a ‘personality test app’, and used the data for targeted political campaigning. This damning revelation is the latest in a series of data misappropriation allegations plaguing Mark Zuckerberg’s tech giant.

As users fumed over the data harvesting scandal, the hashtag #DeleteFacebook started trending on Facebook worldwide. The campaign has gained further momentum after WhatsApp co-founder Brian Acton joined the crowd with the message on Twitter, “It is time. #DeleteFacebook”.
Deleting Facebook will not do much apart from sending a strong message to the social media company. Over the years, Facebook has slowly encompassed our digital lives in such a way that, short of opting out of their entire suite of applications including Instagram, Messenger and WhatsApp, your online activity will still be subject to their data-collection policies. If you are not ready to let go of Facebook but are uncomfortable with the extent of their command over your private information, it might help using existing settings to limit the company’s reach.
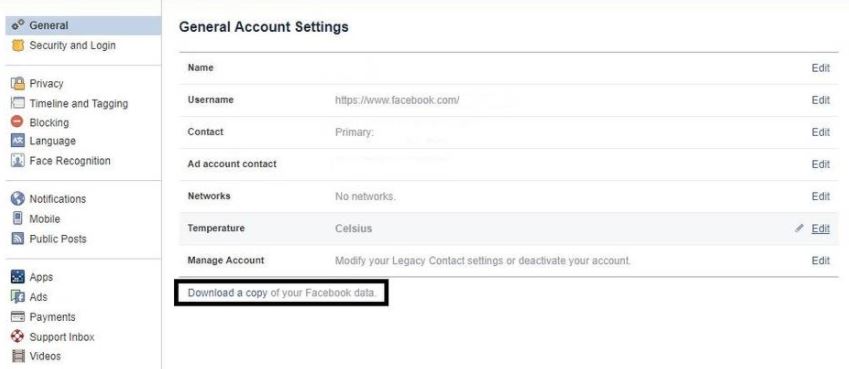
One of the steps to understanding the extent of the issue is seeing the years of data filed meticulously in the Facebook archive. Terms like “meta data” and “purchasing profile” might be familiar to you. To understand this better, information security training professionals said that the first thing you can do is download an archive of your profile on the site. (Settings-General-Download a copy of your Facebook data).
The zip file you download will have complete lists of photographs, videos, statuses, messages you sent and received, and even a record of all the ‘pokes’, among other things. The biggest culprits in data harvesting are third-party apps. As stated in Facebook’s policy page, your information, including “name, profile picture, cover photo, gender, networks, username, and user id are always publicly available to both people and apps. The apps also have access to your friend list and the information you choose to make public.”
To get a better idea of which apps can access your information, go to the Apps section (Settings-Apps) on your Facebook profile. This page will show the apps that have access to your information. You can either revoke the permissions by hovering over the app symbol and clicking ‘Remove’ or can restrict the information you provide to the app by clicking on the ‘Edit Settings’.
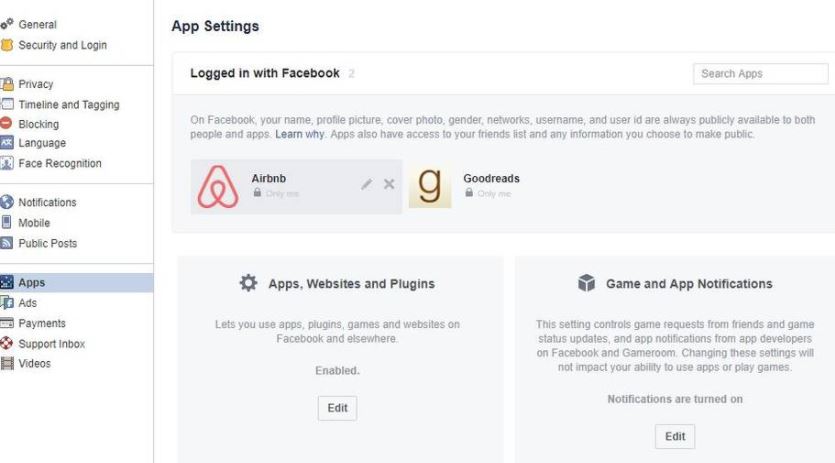
Information security experts explain us that revoking access does not mean that the data that has already been harvested can be removed. For this, you will have to individually contact each of the apps and follow their procedure for data removal.
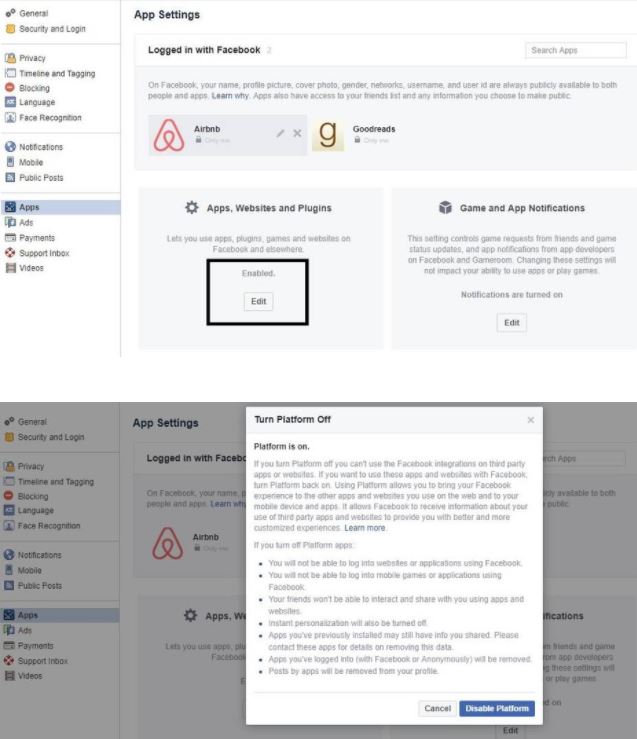
Facebook has made itself indispensable by allowing users to integrate their various accounts by logging into different apps and sites in one touch. This provision can be turned off in the ‘Apps, Websites and Plugins’ section (Settings-Apps-Apps, Websites and Plugins) by clicking on ‘Edit’ and then choosing to disable the platform.
This will mean that you will not be able to play games or log in to websites and applications using Facebook. For instance, after disabling the platform, if you try to log in to a site using the ‘Facebook’ option, you will get a prompt that says “You previously turned off platform apps, websites and plugins”.
You can also use the ‘Apps Others Use’ section to restrict the information that people share when they use apps, games or websites – you can either limit this to basic information like Bio and Birthday, or opt out of it entirely.
At the end of the day, it is important to remember that these are not solutions and can only mitigate the exploitation of our digital footprints. As information security training analyst Frederike Kaltheuner said, what we need is for companies to do better and protect privacy by default, rather than users having to become full-time data protection experts in order to have their basic rights protected.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











