Recently, researchers found that millions of electronic locks installed in hotel rooms are vulnerable to attack. The information security researchers commented that the vulnerabilities found in the computer software meant that they could create “master keys” that opened the rooms without leaving an activity log.
F-Secure’s research team said it had worked with the locksmith over the past year to create a solution to this problem. We know that the Swedish manufacturer is minimizing the risk for hotels that have yet to install an update. “Vision Software is a 20-year-old product that has been compromised after 12 years and thousands of hours of intensive work by two experts at F-Secure,” said a spokeswoman for Assa Abloy.
“These old blocks represent only a small fraction of those that are in use and are being rapidly replaced by new technologies.” The spokesman also commented that the hotels began to implement the solution two months ago. “Digital devices and software of all kinds are vulnerable to piracy, and now it would take a team of expert specialists’ years to try to repeat this.”
The locks of Assa Abloy are used by the largest hotel chains in the world, including Intercontinental, Hyatt, Radisson and Sheraton; it has not yet been revealed which properties still use a compromised version of the Vision by VingCard system.
F-Secure investigators said they started their investigation after a colleague’s laptop was stolen from a hotel room without the thief leaving any sign of unauthorized access.
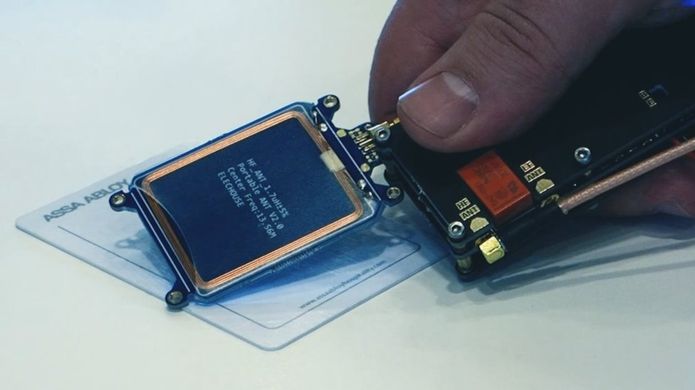
“We wanted to know if it is possible to evade electronic blocking without leaving a trace,” explained Timo Hirvonen, describing the Ghost in the Locks exploit. “Only after thoroughly understanding how it was designed could we identify apparently innocuous faults and find a method to create master keys.”
He also added that the scanned data from any discarded VingCard could be used to mount the attack, even if the access privileges of the card had expired long ago or had been used to open a garage or other parts of the selected hotel instead of a bedroom.
This can also be applied to access other areas of a hotel, including sending an elevator to a VIP floor of a property, if it is protected by the same system, information security experts said. F-Secure said it will not share the hardware and software tools it used to demonstrate its attack on others.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











