Recently a Dutch information security company has discovered that vehicle infotainment systems (IVI) implemented in some Volkswagen Group car models are vulnerable to remote hacking.
Information security researchers from Computest, Daan Keuper and Thijs Alkemade, successfully tested their findings and exploited chains on the Volkswagen Golf GTE and Audi A3 Sportback e-tron models.
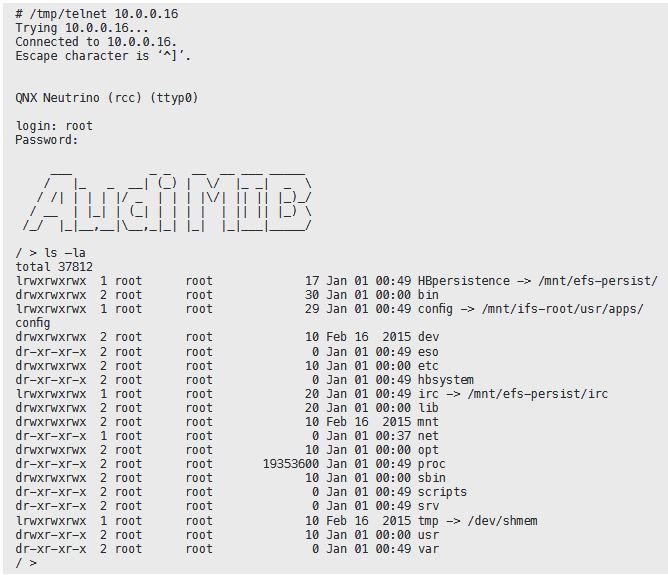
The professionals commented that they used a car’s Wi-Fi connection to exploit an exposed port and gain access to the car’s IVI, manufactured by the company that supplies electronic products Harman.
The experts gained access to the IVI system’s root account, which allowed them to access other automobile data.
“… the attackers could listen to conversations that the driver is carrying out through the car, turn the microphone on and off, as well as access the full address book and the conversation history,” said the Computest researchers.
“Due to the vulnerability, it is also possible to discover, through the navigation system, where the driver has been, and to follow the car live wherever it is at a given moment,” said the information security researchers.
The experts could have done more, but they stopped. Keuper and Alkemade comment that the IVI system is also indirectly connected to the car’s acceleration and braking system, but they stopped investigating for fear that they could violate Volkswagen’s intellectual property.
In addition to the WiFi attack vector, the researchers also found other vulnerabilities that could be exploited through USB debug ports located under the board.
All of these defects were found in July 2017, and they reported all problems to Volkswagen, participating in meetings with the automaker.
“The vulnerability we identified should have been found during an adequate security test,” the experts said. “During the meeting with Volkswagen, it was felt that the reported vulnerability was not yet known, despite being used in tens of millions of vehicles around the world, this IVI system was not subjected to a formal safety test and the vulnerability was still unknown to them.”
Volkswagen already addressed the reported problems, despite the error of implementing an untested system within their cars, Volkswagen worked with the team of information security professionals to address the reported failures.
“The open interface in Golf GTE and Audi A3 was closed with an update of the infotainment software,” the Volkswagen executives wrote in a letter.

Although Volkswagen is closing the vulnerability in today’s information and entertainment systems, professionals are still concerned. This is because the IVI system that they have hacked does not come with a wireless update system, which means that it cannot be updated with a software patch.
On the other hand, in the conversations with Volkswagen, the information security experts comment that the automaker alluded to having solved the failures in the IVI systems that are still in production, but have not yet said how they plan to deal with the already sold cars .
Information security professionals are withholding information about the exploitation of security flaws. The researchers made it clear that they will not reveal the exact services and ports they used to incorporate the VW Golf and Audi A3 models during the experiments.
“We decided not to provide full disclosure of our findings, we describe the process we followed, our attack strategy and the internal parts of the system, but not all the details about remote exploitable vulnerability, as we would consider it irresponsible …” , wrote the researcher in a technical document.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











