On Thursday, Twitter reported that an error caused the passwords of the accounts to be stored in plain text in an internal registry, sending users through the platform struggling to change their passwords.
The company said that its team of information security experts found and solved the problem, also mentioned that its investigation does not show signs of non-compliance or misuse by anyone. The company did not specify how many passwords were affected; Reuters estimated more than 330 million.

“I want to emphasize that this is not a leak and our investigation has not shown signs of misuse,” said a Twitter spokesman. “We are sharing this information so that everyone can make an informed decision about the security of their account,” he added. The spokesman did not comment on the vulnerability and how many users were affected.
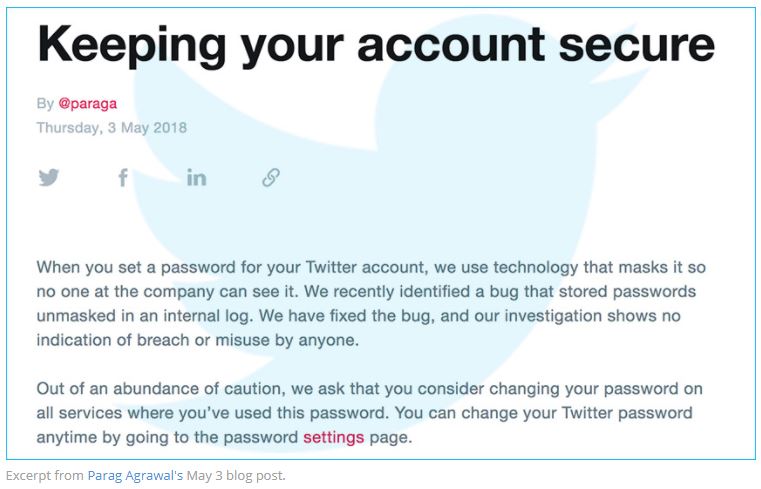
“… Passwords were written to an internal registry before completing the hashing process,” said Parag Agrawal, CTO of Twitter. “This error was found by our security team, we eliminated the passwords and we are implementing plans to prevent this error from happening again.”
All users who opened their accounts on Thursday received a Twitter message asking them to take into account the possibility of changing their password in the services where they used the password.
Twitter commented that it masks passwords using hash using bcrypt, this replaces the real password with a random set of characters stored in your system. However, the vulnerability caused passwords to be written to the company’s internal computer system before the hash process was completed.
Agrawal said Twitter is sharing information about the problem to help users “make an informed decision about the security of their account.”

Information security professional Troy Hunt commented: “The records are often largely automated, but it is certainly a massive oversight,” he said. “For the same reason, if the scope of the problem is that the passwords were captured in the internal records, the records were not exposed and subsequently cleaned up.”
This news is parallel to another incident this week, where Github revealed that he had discovered an introduced vulnerability that exposed a number of user passwords in plain text. GitHub also uses bcrypt for hash passwords, information security experts said.
Twitter attracted attention at the beginning of the week after revealing that it sold access to data to a researcher linked to Cambridge Analytica. This increased the concerns of the security community about how companies protect users’ private information.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











