After an investigation, security professionals have found a backdoor account in the firmware of the D-Link DIR-620 routers; this allows malicious actors to take over any device accessible through the Internet.
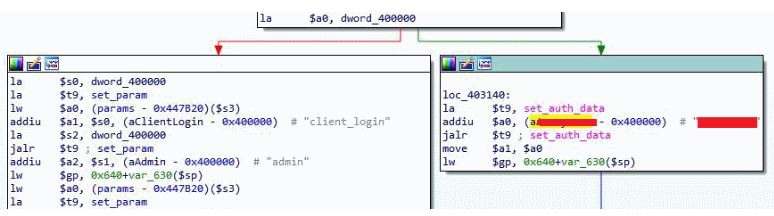
This backdoor, was found by Kaspersky Lab’s information security experts, the backdoor grants access to the device’s web panel, and there is no way that device owners can disable this account.

The way to protect the devices against hacking is to prevent the router from exposing its administration panel in the WAN interface and, therefore, it can be accessed from anywhere on the Internet.
For now, professionals have not revealed the username and password of the backdoor account, this to avoid abuse.
The backdoor account, CVE-2018-6213, is one of the four vulnerabilities found by the information security team in the firmware of these devices. The other three defects include:
- CVE-2018-6210: A vulnerability that allows attackers to recover Telnet credentials
- CVE-2018-6211: an error that allows attackers to execute operating system commands through one of the URL parameters of the administration panel
- CVE-2018-6212: A cross-site scripting vulnerability (XSS) reflected in the “Quick Search” admin panel field of the router
CVE-2018-6210 and CVE-2018-6213 were considered critical vulnerabilities, as they allow attackers easy access to the device.
The D-Link DIR-620 devices are somewhat older router models and there are not many available to exploit, which may be good news.
In general, these devices were implemented by Internet service providers in Russia, the CIS and Eastern Europe, as equipment in the installations for broadband clients.
Most of these devices have been found, and information security professionals have already contacted the ISPs to report the problem.
According to Kaspersky, most ISPs have taken action on warnings and restricted access to these devices on their networks.
Information security experts also contacted D-Link about the problems, but the company commented that it did not intend to issue firmware updates for a previous model.
In the investigation, the following firmware versions of DIR-620 were tested and all were vulnerable to varying degrees: 1.0.3, 1.0.37, 1.3.1, 1.3.3, 1.3.7, 1.4.0 y 2.0.22.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











