This is a tool that allows you to create multiple TOR instances with load balancing traffic between them HAProxy. The tool provides a single endpoint for clients. Also, you can see the TOR processes that are previously executed and create a new identity for selected processes.

According to information security professionals, the tool has been rewritten on the basis of: Multi-TOR Project written by Jai Seidl

As for the load balancing. Multitor uses two different techniques to create a load balancing mechanism: the proxy socks and the http proxy.
To explore websites, for http / https traffic, information security professionals recommend using HTTP proxy. Here, the polipo service is used, which has many useful functions including the cache memory that, in the case of TOR, is not always well directed.
The proxy socks are reliable, but when exploring websites through TOR nodes, it can cause problems.
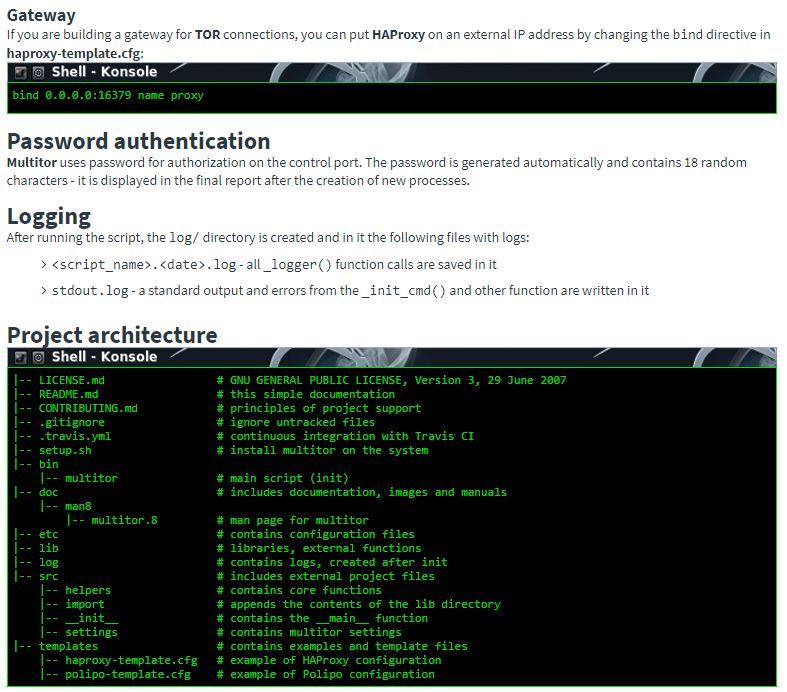
Multitor uses HAProxy to create a local proxy server for all TOR or Polipo instances created and distribute the traffic between them.


In the default configuration, the Polipo cache has been turned off. If you configure the network settings in the browser for traffic to go through HAProxy, information security experts say that you should remember that browsers have their own cache memory, which means that each entry to the page comes from the same IP address. . After clearing the browser cache again, the web server receives the request from a different IP address.
Port numbers for TORs are set by the user using the –socks-port parameter. In addition, the standard port on which HAProxy listens is 16379. Polipo uses 1000 ports smaller than those configured for TOR.
HAProxy statistics interface, if you want to see traffic statistics, go to https://127.0.0.1:16380/stats.
Log in: ha_admin
Password: automatically generated
Polipo configuration interface, if you want to see or change the Polipo parameters, get to https://127.0.0.1:8000/polipo/config

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











