When we talk about banking malwares, better known as banker, we know that their popularity among cybercriminals has decreased; one of the reasons is that antimalware companies and web browser developers are expanding the scope of their protection mechanisms against banking Trojan attacks. According to information securityexperts, this makes banking malware fraud increasingly complicated, which is why malware authors spend their time and resources developing malware that is easier to use and more profitable, such as ransomware, cryptominers and cryptocurrency thieves.

Recently, researchers found a new family of banking malware that uses a new technique to manipulate the browser: instead of using complex process injection methods to monitor browsing activity, this malware engages key window message loop events to inspect the values of the window objects for the banking activity.
When banking activity is detected, the malware injects malicious JavaScript into the web page; this is done through the browser’s JavaScript console or directly in the address bar. Clearly, these operations are performed without the knowledge of the user.
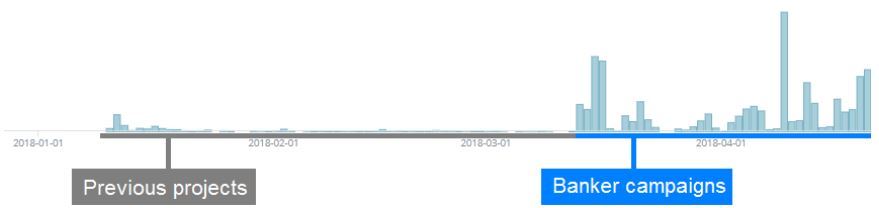
The researchers noted that the group behind this banking malware was spreading earlier projects, earlier this year. The group of information security experts, focused on the clipboard malware for a few months and finally introduced the first version of banking malware, detected by ESET as Win32 / BackSwap.A.
The professionals noticed a huge increase in the detection rate compared to previous projects. The malicious authors have been very active in the development of the banker and have presented new versions almost every day.
The researchers also found that the banker is distributed through malicious email campaigns that carry an attachment of an obfuscated JavaScript download program from a family known as Nemucod.
It is common to see that victim machines are compromised by the Win32 / TrojanDownloader.Nymaim download program, which is distributed using a similar method. Information security professionals still do not know if this is a coincidence or if these two families are directly connected.
The payload is distributed as a modified version of a legitimate application partially overwritten by the malicious load. The application used for the modification is changed regularly.

The application is modified to jump to the malicious code during its initialization.
The method used might remember “trojanization”, but the original application no longer works, and once the control is transferred to the malware, it will never return to the original code. Now, the intention is not to trick users into believing that they are running a legitimate application, but to increase the stealth of malware against scanning and detection. This makes the malware more difficult to detect, since reverse engineering tools like IDA Pro will show the original function main () as a legitimate starting point of the application code and the professional might not notice anything at first sight.
The payload is a position-independent code bubble with the embedded data. Character strings are stored in plain text, since all required Windows APIs are searched by hash during runtime. The malware starts copying itself in a startup folder and then continues with its banking functionality.
Win32 / BackSwap.A show us that in the battle between information security professionals and bank malware authors, new malicious techniques do not necessarily have to be sophisticated to be effective. Experts believe that, as browsers are better protected from the injection of conventional code, malicious actors will attack browsers in different ways and Win32 / BackSwap.A has shown us one of the possibilities.
Researchers have already notified affected browser vendors about the new scripting technique.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











