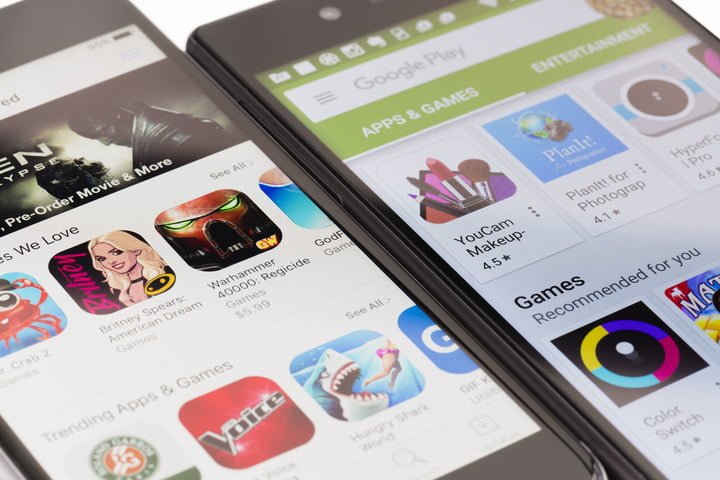
If you were wondering how to receive the latest updates for Android apps installed through a third party, now you can do it directly from Google Play Store.
For security reasons, apps installed from third-party sources couldn’t be automatically updated, since Google doesn’t recognize them as Play Store apps, nor do they appear in the list of apps in your Google account.
Information security training experts say that Google announced a plan to establish an automatic mechanism to verify the authenticity of an app by adding a small amount of security metadata about each package of Android apps distributed by Play Store. These metadata works as a digital signature that would help your Android device verify if the source of an app you installed from an unknown source is a Play Store app and has not been compromised; for example, it would work to prove that a virus is not connected to that app.
Since the beginning of 2018, Google has already started to implement this mechanism, which does not require any action from users or app developers, helping the company to keep smartphone users safe by adding those applications to a user’s Play Store history to drive periodic updates.
In addition, Google announced a new improvement in its plan by adding offline support for metadata verification that would allow Android operating system to determine the authenticity of applications obtained through approved distribution channels by Google Play while the device is offline.
Last year, as part of its mission to protect Android users, Google also added malware protection, called Google Play Protect; according to information security training specialists from the International Institute of Cyber Security, Google Play Protect uses automatic learning and application usage analysis to eliminate potentially dangerous and malicious apps.
Google Play Protect not only scans installed apps from the official play Store, but also monitors applications that have been installed from unknown sources.
Anyway, Play Store is not completely immune to malware; users who do not have the proper preparation in information security training are still recommended to download applications published by certified developers from the app store, in order to minimize the risk of their devices being compromised.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.