Polar, an exercise monitoring gadget and app, joins a long list of devices that would allegedly leak information from its users for security failures, says the International Institute of Cyber Security.
According to pentest experts, the company’s app is so flawed from a security point of view that it is possible to obtain data from the military personnel who use it without major difficulties.
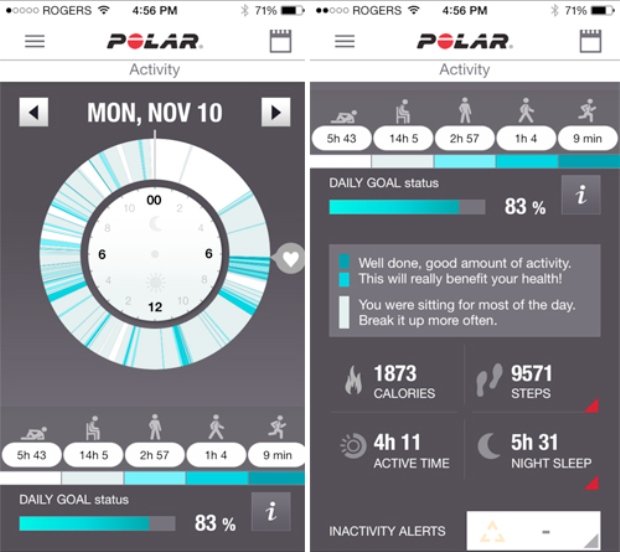
This app allows fitness enthusiasts to measure their time and compare their routines. It is also connected to the company’s heart rate monitor device and the results can be compared with those of others through the social platform Polar Flow, developed by the company itself.
This is where security failures are, especially for people engaged in potentially sensitive occupations, such as the armed forces.
“Displaying all the sessions of a person combined in a single map, Polar not only reveals the heart rhythms, routes, dates, times, duration and rhythm of the exercises performed by individuals in military installations, but also reveals the very same information about their homes, probably” as reported by pentest experts.
According to the research carried out, tracing all this information is very simple through the company’s website; find a military base, select an exercise posted there to identify the attached profile, and see where else that person have performed those routines.
Pentest specialists also added that since fitness apps are normally activated and deactivated at the users’ home, the application would enable people working near sensitive sites with relative ease.
Polar not only makes it relatively easy to see specific people training sessions, but it can also show all the exercises a person has done since 2014 and where those routines have been performed.
Information security specialists illustrated how insecure the app is by showing a map displaying military exercises on a military base in Mali, Africa. They added that it is also possible to individually identify people in the Polar interface, finding their full names and various social network profiles, as well as locating their home addresses.
Researchers have also been able to find on the Polar website records of people exercising in more than 20 sensitive sites (such as homes or military installations), gathering a list of nearly 6K unique users, which marked the places where they work, live and go on vacation.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.