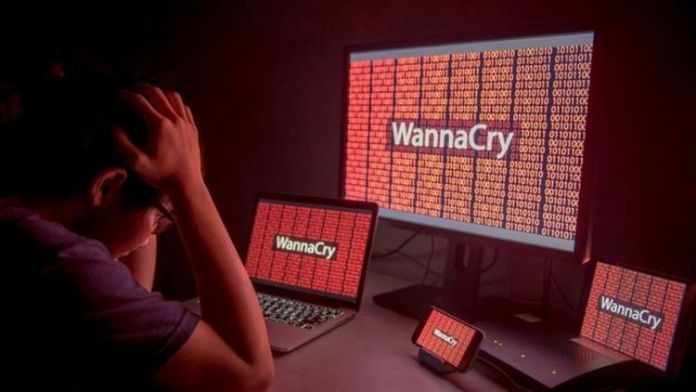
Factories crippled after WannaCry variant infected Windows 7 devices without protection
Enterprise network security specialists from the International Institute of Cyber Security reported that Taiwan Semiconductor Manufacturing Co. (TSMC), the world’s largest chip manufacturer, suffered an infection with WannaCry virus that affected its manufacturing facilities systems, leaving multiple factories unable to function. The event could cost the company over $170M USD.
The company reported that the ransomware outbreak would have a 3% impact on its earnings for the third quarter of the year. TSMC enterprise network security team commented that they also face delays in sending its wafers.
TSMC claims that the WannaCry outbreak was not the work of a hacker. “Data integrity and confidential information were not compromised”, the company’s statement mentions. “This has been our negligence, so we discard any hacker intervention”.
The ransomware continues to harass different organizations. Last March, enterprise network security experts mentioned that an outbreak of malware affected a small number of non-productive systems in Boeing.
TSMC mentions that measures have already been implemented to strengthen their security systems.
As for the outbreak, the company installed a new software tool last Friday, however, it was not confirmed that it was virus-free before connecting to the TSMC network, which allowed the virus to enter the company`s networks.
“In other words, this tool arrived to our facility with a virus already installed”, as mentioned by company’s spokespersons. “The tool was connected to our network without examining it; that was the fault committed by our side. Once in TSMC systems, the WannaCry variant caused our systems to collapse or restart continuously.
The WannaCry outbreak in TSMC is a reminder that patching is not always an easy task in manufacturing environments because any code change should be rigorously tested to ensure that it does not have a real impact, for example in control systems Industrial or monitoring control and data acquisition systems, which control the software and hardware that runs the manufacturing processes. In fact, ICS and SCADA systems can have a life period of 20 to 30 years; many were never designed to connect to the Internet.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.