Cyber security organization specialists from the International Institute of Cyber Security reported the launch of the Lynis security tool. In this new release, several major changes have been made in its central functions. These changes have been made with the purpose of simplifying its use, although there is a possibility of breaking the existing configuration.
Lynis is an open source security scan tool. This software is used by system administrators, cyber security organization professionals and auditors to evaluate the security defenses of their Linux and Unix-based systems. It runs on the host itself, so it performs more extensive security scans than vulnerability scanners.
Supported Operating systems
Lynis runs on almost all Unix-based systems and versions, such as:
- AIX
- FreeBSD
- HP-UX
- Linux
- Mac OS
- Solaris
- And more
It even runs on systems like Raspberry Pi and several storage devices.
Optional installation
According to cyber security experts, Lynis is lightweight and easy to use, plus the installation is optional; just copy it on a system and use the “./lynis Audit system “command to start the security scan. It’s written in a shell script and it was released as open source software.
How does it works
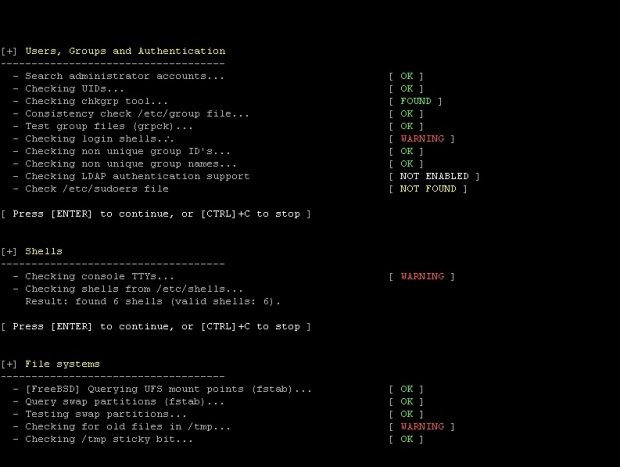
Lynis performs hundreds of individual tests to determine the system’s security status. The security analysis itself consists of performing a series of steps, from the initialization of the program to the scan report.
Steps
- Determine the operating system
- Find tools and utilities available
- Verify the Lynis update
- Run tests from enabled plugins
- Run security tests by category
- Report Status of Security Scan
In addition to the data shown on the screen, all the technical details about the scan are stored in a log file. Any finding (warnings, suggestions, data collection) is stored in a report file.
Opportunistic scanning
Lynis Scan is opportunistic, which means it uses what it can find.
For example, if you see that you are running Apache, you will perform an initial round of Apache-related tests. When the Apache scan also discovers an SSL/TLS configuration, it will perform additional audit steps on that. As you do so, you will collect the uncovered certificates so that they can be scanned later as well.
Use cases
As Lynis is flexible, it is used for several different purposes. Typical use cases for Lynis include:
- Security Audit
- Compliance testing (e.g., PCI, HIPAA, SOx)
- Vulnerability detection and exploration
- System reinforcement
Resources used for testing
Because Lynis is not limited to some common Linux distributions, it uses standard and custom distribution tests that are not found in any other tools.
Lynis complements
Plugins allow the tool to perform additional tests. They can be seen as an extension (or complement) of Lynis, improving its functionality. An example is the compliance check add-in, which performs specific tests only applicable to some standards.
Changelog
## Lynis 2.6.7
### Changed
– BOOT-5104 – Added busybox as a service manager
– KRNL-5677 – Limit PAE and no-execute test to AMD64 hardware only
– LOGG-2190 – Ignore /dev/zero and /dev/[aio] as deleted files
– SSH-7408 – Changed classification of SSH root login with keys
– Docker scan uses new format for maintainer value
– New URL structure on CISOfy website implemented for Lynis controls

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.