Thousands of devices unexpectedly printed a message supporting PewDiePie
Cybersecurity and digital forensics specialists reported that during the most recent months a “Youtube war” has been waged pursuing the recognition of the channel with the most subscribers between the Swedish YouTuber Felix “PewDiePie” Kjellberg, and the firm T-Series, channel dedicated to Bollywood cinema.
This is not a minor recognition, even PewDiePie fans have designed a campaign known as “Bro Army”, designed to ‘recruit’ friends and family members of the Swedish vlogger subscribers, in order to keep him at the top of the video platform.
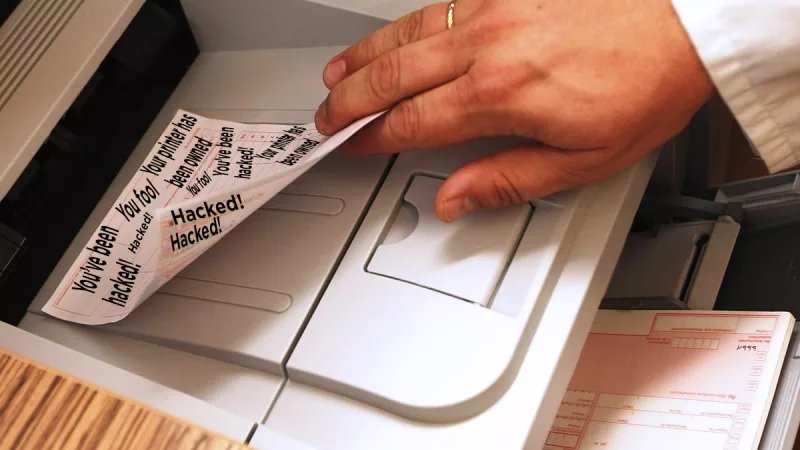
But this dispute has reached new and unthinkable levels. Digital forensics specialists from the International Institute of Cyber Security report that some person or group hacked printers from around the world to print propaganda in favor of PewDiePie. Twitter users everywhere shared their experiences with the incident in the past few days.
“The message appeared unexpectedly in our printer. I think PewDiePie hacked our systems”, mentioned the Twitter user DrMoxmo, attaching a photo of the message that appeared when using a printer.
According to specialists in digital forensics, the printers were, indeed, hacked, although it is not PewDiePie who is behind this incident. Through a Twitter account, identified as TheHackerGiraffe, the attacker or attackers mentioned some details about this incident:
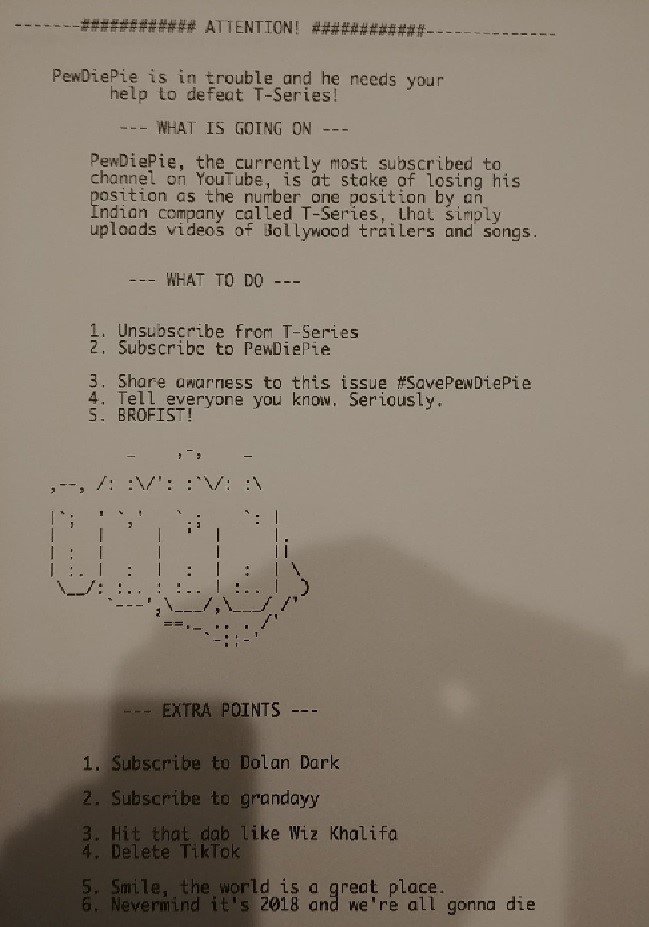
“This is how the PewDiePie printer hack happened:
- I was bored after playing Destiny for 4 hours in a row and decided I wanted to hack something. So I thought of any vulnerable protocol I could find in Shodan
- While playing with Shodan, it occurred to me that I could hack printers from around the world to printed anything
- I was horrified to find over 800k vulnerable ports. I chose the first 50k printers I found running on port 9100 and downloaded the list of Shodan
- After thinking what message I could print, it occurred to me that it would be best to print a message in support of PewDiePie
After I left the script running, I did this Twitter account, other one on Reddit, and I waited for people to find me.”
According to reports of experts in digital forensics, the hacker used a tool called PRET, a printer exploit rootkit, which, according to GitHub, allows hackers to “capture, manipulate, or print jobs to access file systems and device memory, with the possibility of damaging the hardware as well.”
The hacker claims that he did not act with any malicious purpose, but did so to raise awareness of printer users about how vulnerable these devices can be. “People underestimate the ease with which a hacker could exploit these vulnerabilities; I could have stolen files, installed malware or even caused physical damage to any device. The worst thing is that downloading, creating and executing these scripts took me less than half an hour.”
Experts in digital forensics recommend applying some security measures to prevent this type of attack; properly configuring a firewall, changing the default password or even turning off your device when you do not use it can help you to stay safe from some attack vectors.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.